What is CMMC 2.0, and How Does it Differ from CMMC 1.0?
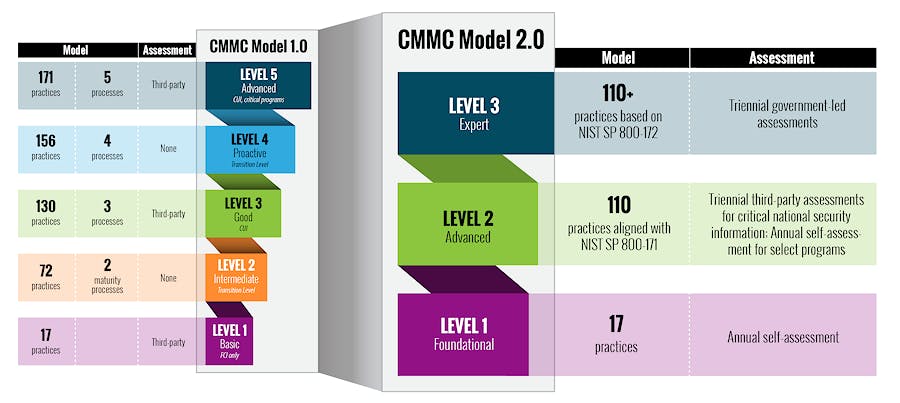
The Cybersecurity Maturity Model Certification (CMMC) 2.0 is the Department of Defense’s (DoD) latest cybersecurity framework designed to protect the Defense Industrial Base (DIB). It replaces CMMC 1.0, streamlining compliance while maintaining stringent security measures.
Key changes include:
- Reduction from five to three compliance levels.
- Introduction of self-assessments for lower compliance levels.
- Implementation of Plans of Action and Milestones (POA&Ms) for remediation.
- Removal of unique CMMC practices in favor of greater alignment with existing NIST 800-171 and 800-172 cybersecurity standards.
Understanding the Importance of CMMC 2.0 for Defense Contractors
CMMC 2.0 is essential for defense contractors as it strengthens national security by safeguarding Controlled Unclassified Information (CUI) and Federal Contract Information (FCI). Compliance helps protect the DIB from evolving cyber threats, reducing the risk of data breaches that could compromise sensitive research, supply chain integrity, military operations, and critical infrastructure. Failure to comply may lead to loss of contract opportunities and reputational engineering data, mage, as well as potential legal and regulatory consequences (e.g., lawsuits, fines, etc.)
What is Controlled Unclassified Information (CUI)? | What is Federal Contract Information (FCI)? |
Controlled Unclassified Information (from 32 CFR 2002.4) is “information the Government creates or possesses, or that an entity creates or possesses for or on behalf of the Government, that a law, regulation, or Government-wide policy requires or permits an agency to handle using safeguarding or dissemination controls. However, CUI does not include classified information or information a non-executive branch entity possesses and maintains in its own systems that did not come from, or was not created or possessed by or for, an executive branch agency or an entity acting for an agency.” | Federal contract information (from 48 CFR 52.204-21) means “information, not intended for public release, that is provided by or generated for the Government under a contract to develop or deliver a product or service to the Government, excluding information provided by the Government to the public (such as that on public websites) or simple transactional information, such as necessary to process payments.” |
All CUI in possession of a Government contractor is FCI, but not all FCI is CUI.
CMMC Certification Process
Starting November 10, 2025, new DoD solicitations may include CMMC 2.0 requirements, with full phased implementation continuing through 2028. Achieving CMMC 2.0 certification follows a structured process that varies by required compliance level. Below is a step-by-step breakdown of the certification process:
| Phase | Start Date | What Gets Rolled Out |
Phase 1
| Nov 10, 2025 | Inclusion of Level 1 (self) or Level 2 (self) CMMC requirements in new contracts. DoD retains discretion to require Level 2 third-party (C3PAO) in some solicitations. |
| Phase 2 | Nov 10, 2026 | Required Level 2 certification (C3PAO) for applicable new contracts. |
| Phase 3 | Nov 10, 2027 | Extension of Level 2 C3PAO requirement to contract option periods + introduction of Level 3 (DIBCAC) assessment requirements. |
| Phase 4 | Nov 10, 2028 | Full implementation: all applicable solicitations and contracts (including option periods) will require a CMMC level. |
Note: There is no grace period. Contractors must meet the required CMMC level, or be in an approved self-assessment, when the clause is added to the contract.
Assessment Types & Validity
- Level 1 (Self): FCI only; self-assessment
- Level 2 (Self): CUI (non-critical); self-assessment
- Level 2 (C3PAO): CUI (sensitive); third-party assessment
- Level 3 (DIBCAC): Very high-value CUI; DoD-led assessment
Assessment validity, POA&Ms, and affirmation requirements follow the same structure you previously described, but with the timeline now live.
How to Act Now for CMMC Compliance
Since the rule is in force, here’s what contractors should be doing today:
Determine Your Required CMMC Level
- Identify if your company handles FCI or CUI.
- Review contractual requirements to determine if you need Level 1, Level 2, or Level 3 compliance.
Conduct a Gap Analysis
- Compare your existing cybersecurity controls against NIST 800-171 (for Level 2) and NIST 800-172 (for Level 3).
- Identify weaknesses and create a remediation plan.
Develop and Update Documentation
- Prepare a System Security Plan (SSP) detailing your cybersecurity policies.
- Establish an incident response plan, risk management framework, and audit logs for tracking compliance.
Implement Remediation Actions
- Implement necessary security controls, policies, and procedures to close identified gaps.
Prepare Assessment
- Partner with a C3PAO and schedule your third-party assessment by a CMMC C3PAO to conform to higher levels of CMMC 2.0 compliance.
Stay Updated
- Continuous monitor, review, and update security controls, and documentation.
- Follow DoD announcements and updates regarding compliance requirements.
How can Echelon Risk + Cyber can help
Successfully preparing for CMMC 2.0 requires more than just checking boxes, it takes a structured approach, expert guidance, and ongoing support to ensure your organization is fully audit-ready.
Echelon’s CMMC 2.0 Compliance Service provide end-to-end assistance for defense contractors, guiding you through every step of the compliance journey.
From defining scope and conducting gap assessments to implementing remediation strategies, performing pre-audit validations, and supporting official assessments, our certified practitioners ensure your team is prepared, confident, and positioned to maintain long-term compliance.
Final Thoughts
CMMC 2.0 represents a significant shift in DoD cybersecurity compliance, offering greater flexibility and alignment with existing NIST frameworks. Although challenges exist, particularly for small businesses, strategic planning, leveraging external support, and prioritizing cybersecurity best practices can facilitate a smoother compliance process. Organizations should also stay updated on DoD guidance and regulatory changes as CMMC 2.0 continues evolving.
Contractors, with assistance of key partnerships like Echelon Risk + Cyber, should begin preparations now to ensure seamless compliance before full implementation.
Early adoption of cybersecurity best practices can provide a competitive advantage, ensuring continued eligibility for DoD contracts and strengthening overall cyber resilience.
Resources
- ISI. (2025, February 3). CMMC 2.0 updates: The latest contractors need to know. ISI.
- U.S. Department of Defense. (2021, December 2). Cybersecurity Maturity Model Certification (CMMC) Model Overview Version 2.0.
- Casey, D. (2020, June 19). FCI and CUI, what is the difference? CUI Program Blog. National Archives and Records Administration.
- U.S. Department of Defense. (2023). 32 CFR § 170.16 – CMMC Level 2 self-assessment and affirmation requirements. Electronic Code of Federal Regulations.
- CrowdStrike, Inc. (2024). Navigating the Complexities of CMMC 2.0 Compliance [Data sheet]. CrowdStrike.