Welcome to our weekly newsletter where we share some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
To receive these and other curated updates to your inbox on a regular basis, please sign up for our email list here: https://echeloncyber.com/ciw-subscribe
Also, we are always looking for great people to join our team. If you know anyone who fits the profiles for any of our open positions, drop me a line and let me know!
Before we get started on this week’s CIW, I’d like to invite you to join us on April 18th for an insightful webinar on how to improve your organization's cybersecurity posture in the long term. Many companies assume that simply checking the boxes to achieve compliance means they are secure, but this is a common mistake.
During this webinar, Kaushik Kiran, Director of vCISO services at Echelon Risk + Cyber, and Alev Viggio, Director of Compliance at Drata, will provide valuable tips on how to transition to a risk-based approach to compliance. You'll learn how to identify risk areas for your company, improve data visibility through a risk and compliance lens, quantify business risks by using a common framework, and identify and quantify KPIs.
By attending this webinar, you'll gain the knowledge and insights you need to stay one step ahead of risks and achieve true security for your organization. Don't miss this opportunity to learn more about cybersecurity, compliance, and risk management. Register now using the link below!
Register Here: https://drata.com/resources/webinars/beyond-achieving-compliance

Away we go!
1. Air National Guardsman Arrested in Pentagon Classified Document Leak
Federal investigators arrested a member of the air national guard on Thursday, who they say is connected to a massive leak of classified U.S. intelligence materials that have caused tensions with American allies and exposed flaws in Ukrainian military defenses. The air national guard member, a 21 year old, has been identified as Jack Teixeira by The New York Times. He is a member of the Massachusetts Air National Guard's intelligence branch and is connected to the internet community, where the stolen data first surfaced.
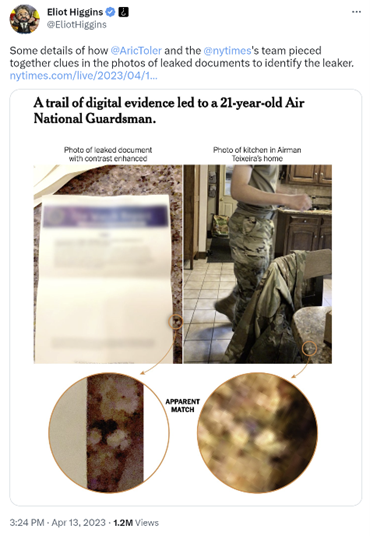
The FBI, the New York Times, and Bellingcat, an internet sleuthing community, among others, collaborated to identify the suspected Pentagon leaker, Jack Teixeira. The private Discord server where Teixeira submitted secret information became public knowledge thanks to Bellingcat. The 21-year-old defendant's social media profile was linked to pictures of the Teixeira family kitchen, where the top-secret documents are allegedly depicted. Bellingcat and the Times declined to comment on if or when they informed federal authorities of their discoveries during the reporting process before Teixeira's arrest on April 13. The incident has exposed serious flaws in the US government's handling of sensitive data, and experts have warned that the nation's cyber infrastructure is dangerously flawed to allow such breaches.
The files Teixeira accessed were stored on what is known as the Joint Worldwide Intelligence Communications System, a 30-year-old system that originally handled materials produced by the intelligence community for distribution among a much smaller segment of the defense department. Many say that the agencies are lagging in their ability to modernize systems like the Joint Worldwide Intelligence Communications System, particularly as the volume of intelligence they are meant to hold has exponentially increased.
2. Samsung Employees Leaked Sensitive Data to ChatGPT
Three different instances of engineers from Samsung Electronics leaking private company information through ChatGPT demonstrate the necessity for workplace rules governing employees' use of AI technologies.
In the first case, an engineer pasted flawed source code from a semiconductor database into ChatGPT, and in the second, a worker entered code to find flaws in specific Samsung products. An employee requesting ChatGPT to create minutes of a Samsung internal meeting led to the third leak. All of the data shared into ChatGPT becomes the property of OpenAI and is used as training data for the huge language/machine learning model, also making it potentially retrievable with the right instructions.
The occurrences shed more light on the dangers that cybersecurity experts have been warning of. Samsung initially banned the technology before granting employees access to it, but has since reportedly limited its internal use by limiting the length of the questions asked. The company is also reportedly considering disciplinary punishment against staff members who divulge company information with Large Language Models (LLMs) like ChatGPT.
Security experts have cautioned that when employees start using ChatGPT for a variety of reasons within the enterprise, a tendency already shown in many studies earlier this year, such leaks could become common.

3. First-of-Its-Kind Cybersecurity Guidance Urges Secure-by-Design Software
The Cybersecurity and Infrastructure Security Agency (CISA), alongside other international cybersecurity authorities, has published the first-ever joint guidance for software manufacturers in creating software products that are secure-by-design and secure-by-default. The new guidance, entitled “Shifting the Balance of Cybersecurity Risk: Principles and Approaches for Security-by-Design and -Default,” is intended to catalyze progress towards achieving a safe and secure future.
The guidance is ultimately based on four core principles that urge software manufacturers to build software security into their design processes before developing, configuring, and shipping their products. These principles include taking ownership of the security outcomes of their technology products, shifting the burden of security from customers, embracing radical transparency and accountability, and building the right organizational structure by providing executive-level commitment for software manufacturers to prioritize security as a critical element of product development.
Cyber authorities from around the world, including, Australia, Canada, the United Kingdom, Germany, the Netherlands, and New Zealand, co-authored the guidance with CISA, the Federal Bureau of Investigation (FBI), and the National Security Agency (NSA). The main crux of the guidance is to give software manufacturers the guidance they need so that they may integrate security into the earliest phases of design to build a secure and resilient technology ecosystem.
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about