Welcome to our weekly newsletter where we share some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
To receive these and other curated updates to your inbox on a regular basis, please sign up for our email list here: https://echeloncyber.com/ciw-subscribe
Before we get started on this week’s CIW, I’d like to highlight a Senior Cyber Advisory Consultant role opening on our Strategic Cybersecurity Advisory team! This is an excellent opportunity to join a growing team and work on a variety of exciting client engagements. Interested in applying, click here.

Away we go!
1. Double the Supply Chain Attack, Double the Fun!
As we reported a few weeks ago, a new software supply chain compromise was discovered in the enterprise software, 3CX Desktop App. The compromised software contained a trojanized version of the legitimate software that was available for download from the company's website.
There have been new developments from Mandiant, who recently responded to the incident and identified that the initial compromise vector of 3CX's network originally occurred via malicious software downloaded from Trading Technologies. You heard that right, a nested supply chain attack! This is the first time that Mandiant has seen a software supply chain attack lead to another software supply chain attack.
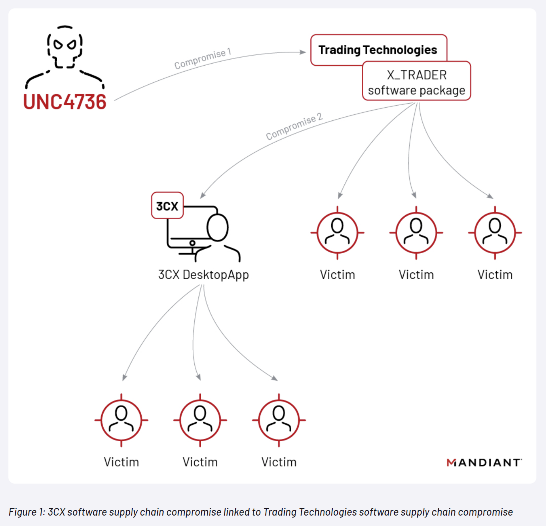
The investigation by Mandiant uncovered that the initial intrusion vector was a malware-laced software package distributed via an earlier software supply chain compromise that began with a tampered installer for X_TRADER, a software package provided by Trading Technologies. The compromised X_TRADER and 3CX Desktop App applications both contained, extracted, and ran a payload in the same way, although the final payload was different. This suggests that the same threat actor or group was behind both attacks.
Mandiant researchers suggest that UNC4736 demonstrates varying degrees of overlap with several North Korean operators tracked by their intelligence group. Eventually, the threat actors were able to take over the build environments for both Windows and macOS. The attackers were also able to move laterally within the 3CX organization using a compiled version of the publicly available Fast Reverse Proxy project.
The attack highlights the importance of supply chain security and the need to implement robust measures to prevent such attacks. It also emphasizes the need for organizations to monitor their networks regularly for any suspicious activity and to have a response plan in place in case of a suspected breach.
2. Western Digital Faces Extortion Attempt After Hackers Steal 10 Terabytes of Data
Data storage giant Western Digital was recently hit by hackers who stole roughly 10 terabytes of data, including sensitive customer information. The threat actors are now demanding a ransom of at least eight figures in exchange for not publishing the stolen data. The hackers claim to have stolen data from several of the company's systems, including its SAP Backoffice instance and a Box account. They were also able to steal data from an internal email system and a PrivateArk instance, a cybersecurity product.
Western Digital initially disclosed a network security incident on April 3, stating that hackers had exfiltrated data from several of its systems. However, the company did not provide any specific details about the stolen data, noting only that it was working to understand the nature and scope of the breach. A hacker who claims to have stolen the data recently spoke to TechCrunch, sharing a file digitally signed with Western Digital's code-signing certificate, showing they could now impersonate Western Digital.

The hackers claim that they are only seeking to make money from Western Digital, but they have threatened to publish the stolen data on the website of a ransomware gang called “Alphv” if their ransom demands are not met. Per the TechCrunch story, the hackers state they are still dug into the network and could exert control over systems if the company doesn’t comply with their demands.
3. March 2023 Sees Highest Number of Ransomware Attacks in Three Years
According to the NCC Group’s March 2023 Cyber Threat Intelligence report, March 2023 has set a new record in ransomware attacks. The analysts at NCC Group recorded 459 ransomware attacks, marking a 91% increase from February 2023 and a 62% increase from March 2022.
Much of this spike in activity is attributed to a vulnerability in Fortra's GoAnywhere MFT secure file transfer tool that was exploited by the Clop ransomware gang as a zero-day to steal data from 130 companies within ten days. Clop performed 129 recorded attacks last month, topping NCC Group's graph with the most active ransomware gangs for the first time in its operational history.
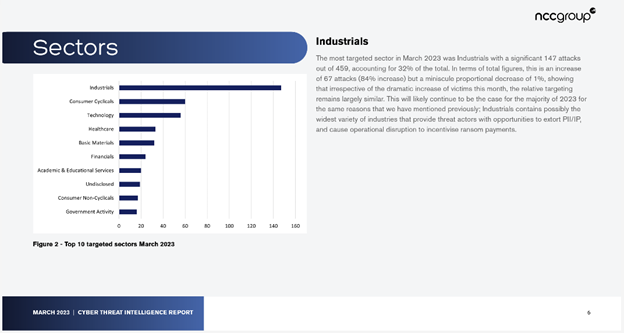
Per the NCC report, the industrial sector was the most targeted in March, accounting for 32% of the recorded attacks. Other sectors that received significant attention from ransomware gangs are "Technology," "Healthcare," "Basic Materials," "Financials," and "Educational Services." The report highlights strong controls and mitigating factors, such as the importance of applying security updates as soon as possible, implementing additional measures to mitigate potentially unknown security gaps, and monitoring network traffic and logs for suspicious activity.
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about