Welcome to our weekly newsletter where we share some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
To receive these and other curated updates to your inbox on a regular basis, please sign up for our email list here: https://echeloncyber.com/ciw-subscribe
Also, we are always looking for great people to join our team. If you know anyone who fits the profiles for any of our open positions, drop me a line and let me know!
Before we get started on this week’s CIW, I’d like to highlight the fact that we have several career openings to join our growing team. Echelon is growing at a rapid pace, which provides a ton of opportunity for growth and development in your career. For example, we are looking for someone who is passionate about Incident Response Planning and Preparedness to help us lead our offerings in that space, a Senior Consultant on the Offensive Security side to lead advanced adversarial emulation exercises, and a Senior Security Consultant to help lead all types of cyber and privacy compliance initiatives! Please visit our LinkedIn Jobs Board to apply today!
Away we go!
1. A Peek into Microsoft’s Microsoft Offensive Research & Security Engineering (MORSE) Team
Microsoft recently published a blog post about their internal security team that is tasked with hunting and fixing coding issues before the bad guys do. Microsoft famously (or infamously, depending on how you look at it) releases a slew of patches on the second Tuesday of each month, known as Patch Tuesday. This is in an effort to locate, remediate and tell the world to patch flaws found in previously released code. This is an important process because billions of people around the world rely on the Microsoft operating system suite to run their digital lives. It’s also no secret that hackers and researchers are finding serious flaws at a rate that is faster than ever seen before.

These types of problems need unique solutions, especially when you are dealing with the scope and scale of Microsoft and all the code that they support. The MORSE team at Microsoft is a multidisciplinary team made of read teamers (the breakers), blue teamers (the defenders), and green teamers (the builders/fixers) that work together to actively hunt down issues and fix them before the bad guys do.
Justin Campbell, principal security software engineering lead at Microsoft Security said in the blog post, “We aren’t just a red team where we come in and find bugs. We don’t just wait for an external entity to tell us there’s a bug. We have a group that is the right balance of self-sufficiency to identify issues, react and then make investments in the product. This isn’t just traditional bug hunting.”
This is a very interesting look into how one of the top tech firms in the world goes about code security and bug management, very interesting read.
2. Scammers Sent Uber to Take Elderly Lady to the Bank
In a chilling recent blog post from Brian Krebs, he details a hackers attempt to stealing an elderly woman’s money by going as far as buying her an Uber to her bank because she didn’t drive. The mother of Travis Hardaway, a former music teacher turned application developer, said that his mother received a fake email pretending to be from Best Buy.

The fraudsters claimed to have accidentally sent too large of a refund to the woman’s bank account and that the man responsible was going to face some dire consequences if the money wasn’t returned timely. When the fraudsters learned that Mrs. Hardaway didn’t drive, they sent her an Uber.
Luckily, she grew exasperated of the efforts and went to a neighbor’s house who helped identify the scam. These types of stories highlight examples of exactly how far fraudsters will go to separate victims, especially the elderly, from their hard-earned income. The elderly are ripe targets for these types of schemes because they are so vulnerable and not tech-savvy and this creates a massive issue that not enough people are trying to solve.
3. Another Rough Week for Web3, Dual Hacks Causing Havoc
With the rise of cryptocurrency over the past few years, there has been an increase in threat actors looking to for ways to exploit weaknesses in the systems that control and interact with the blockchains that hold cryptocurrencies and other assets like NFTs.

This year has been a doozy so far with Axie Infinity’s Ronin Bridge ($600 million lost in a hack in April) and Harmony’s Horizon bridge ($100 million lost in a hack in June). This past week saw a double gut punch.
First was to the Nomad Bridge, who lost nearly $150 million in a reported hack. Nomad, who describes itself as, “a security-first cross-chain messaging protocol” on its website was drained of their crypto assets. Samczsun, a researcher for Paradigm outlined his probable cause for the hack on his Twitter account. As Samczsun puts in, “A routine upgrade marked the zero hash as a valid root, which had the effect of allowing messages to be spoofed on Nomad. Attackers abused this to copy/paste transactions and quickly drained the bridge in a frenzied free-for-all.”
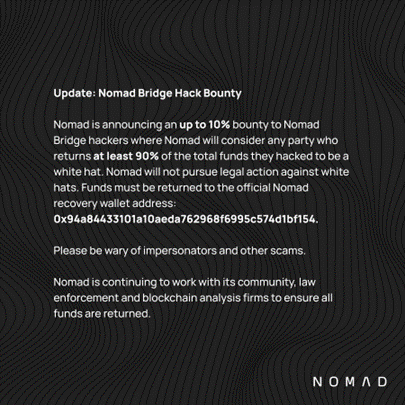
Nomad is now asking for the cryptos assets back, noting that they will consider any one who does as a “White Hat” who was doing so to protect the assets. I guess this is the crypto version of tackie-backsies?! To date, they have noted on their Twitter page that $32 million has been returned thus far.
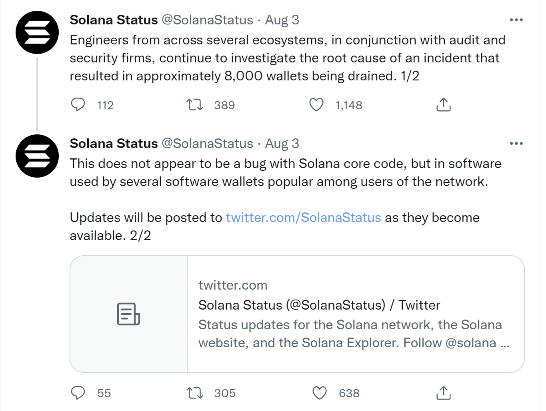
If that weren’t enough, nearly 8,000 Solana wallets were drained of their assets. Blockchain fraud analysts at Elliptic have put the stolen asset tally at $5.8 million thus far. The issue doesn’t appear to be with the Solana blockchain itself but with the hot wallets that connect to it (Slope and Phantom). In the case of Slope, it appears that they were logging the mnemonic seed phases in clear text to their logging server, allowing the hackers to drain the wallets. A mnemonic phrase is a list of words that store all the information needed for the recovery of a crypto wallet. That’s probably not a good thing to store in clear text?
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about