Welcome to our weekly newsletter where we share some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
To receive these and other curated updates to your inbox on a regular basis, please sign up for our email list here: https://echeloncyber.com/ciw-subscribe
Before we turn to this week’s edition of Cyber Intelligence Weekly, I want to introduce a new CISO Spotlight Series: The Human Side of Cybersecurity.
This series is grounded in conversation rather than commentary. It centers on CISOs who are in the seat—navigating real leadership pressure, complex risk decisions, and the human realities of building and sustaining security programs. Some are earlier in their journey, others further along paths many of you may recognize or aspire toward. What they share isn’t theory. It’s experience—earned through moments of progress, frustration, growth, and reflection. These conversations are for the professionals who show up every day to quietly carry the weight of this industry.
Aaron Stanley (dbt Labs) — “Play the long game.”
In this episode, I sat down with Aaron Stanley, CISO at dbt Labs, whose career spans government work, incident response, consumer tech, and high-growth SaaS. What keeps pulling him back into cybersecurity isn’t the technology—it’s a deep-rooted belief in privacy, individual rights, and the role security plays in protecting how people live and work in a digital world.
One of the most honest moments in our conversation came from a hard leadership lesson. Aaron watched an entire application security team unravel in a single quarter. The reset that followed reinforced a critical principle: security can’t be treated as “just engineering.” Technical skills matter, but successful programs require a security-first mindset and a focus on culture, mission, and business impact.
He also challenged a few industry norms. Aaron is skeptical of heavy investment in “gotcha” phishing simulations and believes we often over-engineer identity by chasing static least-privilege models. His perspective: shift toward zero trust and just-in-time access, where permissions are dynamic and aligned to real-time need.
His billboard message for CISOs is simple and powerful: Play the long game. Real security maturity isn’t built in quarters—it’s built over years of steady cultural change.
Additional takeaways from the conversation:
- Burnout isn’t about hours — it’s about impact. Teams burn out when they feel like nothing changes, not when they’re simply busy.
- Culture is the real control. The goal isn’t to “do security” — it’s to embed security into how the business operates.
- CISOs spend more time on people and business than technology. Budgeting, alignment, communication, and influence dominate the role.
- No one knows the perfect answer. Security leaders are building the airplane mid-flight—there is no universal playbook.
- Threat models matter more than trends. What’s “overhyped” depends entirely on the risks your organization actually faces.
- Visibility and storytelling prevent burnout. Regularly showing the company how security creates value increases engagement and meaning for the team.
- Community is a competitive advantage. Unlike many executive roles, security leaders can openly share failures and lessons with peers.
If you’re leading a program—or aspiring to—this conversation is a reminder that the job isn’t about tools. It’s about influence, patience, and building something that lasts.
🎥 Watch the full conversation here: https://www.youtube.com/watch?v=x59YihD2siQ

_________________________________
RSA 2026, Come Meet With Us!
Also, to highlight upcoming events, we hope to meet you at RSAC 2026! If you are heading out to RSA and want to meet up with the Echelon team, come see us at our exclusive happy hour at the prestigious Olympic Club, a quiet oasis from the busy hustle and bustle of RSA.
Join Echelon Risk + Cyber for our annual RSA Happy Hour at The Olympic Club on Monday, March 23, from 3:00–5:00 PM PT, just before the official RSA Welcome Reception, with our sponsors Drata and Schellman!
Good people, great conversations, easy networking, no pressure.
📍 The Olympic Club, San Francisco
👉 Reserve your spot here: https://lnkd.in/enj3Q9D3
Away we go!
1. Notepad++ Update Hijack: A Supply-Chain Reminder for Every Security Team
Over the past week, Notepad++ maintainers confirmed a supply-chain incident that didn’t stem from a bug in the editor’s source code, but from a compromise upstream in the infrastructure that delivered updates. The core allegation is simple and ugly: for a period of time, some users requesting update information were selectively redirected to attacker-controlled resources, meaning the “trust me, I’m an update” moment became the attacker’s distribution channel. Rapid7 characterized it as a compromise of the infrastructure hosting Notepad++ that was then used to deliver a previously undocumented backdoor they dubbed Chrysalis, and they tie it to a long-running China-nexus threat cluster they track as Lotus Blossom.
The mechanics matter because they look like a playbook we keep seeing: attackers don’t need to win against every endpoint if they can win once against a choke point. In Rapid7’s investigation, telemetry shows Notepad++ launching its updater (GUP.exe), followed by execution of a suspicious update.exe downloaded from 95.179.213.0—a breadcrumb that turns a routine update check into a potential beachhead. From there, the campaign reportedly used staged loaders and sideloading techniques to unpack and run the backdoor, blending custom tooling with commodity tradecraft to stay resilient against straightforward detections.
The Notepad++ team’s response focuses on hardening the update trust chain—exactly where this kind of intrusion hurts most. In v8.8.9, they tightened WinGUp’s behavior to verify both the certificate and signature of downloaded installers and to abort updates if verification fails, while they continue investigating the precise traffic-hijack method. Kaspersky’s parallel write-up adds technical depth and reinforces the bigger takeaway: “update integrity” isn’t a checkbox; it’s a system of controls—cryptographic verification, signed metadata, secure hosting, and monitoring that treats update paths like production-critical assets.
For defenders, the lesson isn’t “panic about Notepad++”—it’s to assume that widely trusted distribution channels will be targeted precisely because they’re trusted. If your environment allows user-installed tools (or relies on third-party updaters), you want layered controls: application allowlisting, tighter egress filtering, TLS inspection where appropriate, EDR analytics for suspicious parent/child process chains (updater → unknown installer), and threat hunting keyed off published IoCs when reputable teams provide them. In other words: treat software updates as a privileged pathway, because attackers already do.

Phishing Campaign Abuses Google Cloud Application Integration
A sophisticated phishing campaign discovered in late 2025 is notable for how it weaponizes legitimate cloud services to increase trust and bypass traditional email defenses. Researchers found attackers abused Google Cloud Application Integration’s “Send Email” task to send nearly 9,400 phishing emails to roughly 3,200 organizations worldwide. By using a legitimate Google-owned address and system notification format, these phishing messages — mimicking voicemail alerts and file access requests — were far more likely to evade detection and land in inboxes.
From a governance perspective, this incident illustrates the risk of service abuse threats (MITRE ATT&CK T1566.002) where automation features become delivery mechanisms. Security teams should recognize that SPF/DMARC/DKIM validation alone no longer suffices when trusted cloud automation tools can send messages with valid authentication.
For cloud security compliance, this underscores the importance of least-privilege controls and granular automation governance. Ensuring that only authorized workflows can trigger high-impact actions such as “send email” — and monitoring those actions — can reduce attacker leverage. Multi-factor authentication and behavioral analytics are also critical to detect anomalous use of legitimate platforms.
Finally, this campaign highlights the need for security awareness training tailored to cloud-originated notifications, as user trust in recognizable domains is a key factor in credential harvesting success. Regular phishing simulations that incorporate service abuse scenarios will help raise resilience against these advanced threats.

2. CISA’s New Directive Sends a Clear Message: Unsupported Edge Devices Are a Cyber Liability
Federal agencies just received a blunt reminder of a risk many organizations quietly live with every day: unsupported infrastructure is an open door. In a new Binding Operational Directive (BOD 26-02), the Cybersecurity and Infrastructure Security Agency (CISA) ordered agencies to identify and remove network edge devices that are no longer supported by vendors. The concern is straightforward—routers, firewalls, VPN appliances, and other perimeter systems that don’t receive security updates have become prime targets for nation-state and advanced threat actors looking for a foothold inside government networks.
CISA’s timeline is aggressive but practical. Agencies must quickly update any device that can still be brought back into a supported state, report their inventory of end-of-support (EOS) edge devices within three months, and begin decommissioning them over the next year. Within 18 months, all unsupported edge systems must be removed, and within two years, agencies are expected to have lifecycle processes in place to prevent the problem from happening again. The directive also requires organizations to identify devices that will become unsupported soon—pushing lifecycle management from a reactive cleanup exercise into an ongoing discipline.

The urgency reflects what threat intelligence teams have been seeing for years: attackers love the edge. These devices sit at the boundary of the network, often have deep integration with identity and access systems, and are frequently overlooked in patching and monitoring programs. Once compromised, they provide a quiet path for persistence, credential harvesting, and lateral movement. Many high-profile intrusions in recent years have followed exactly this playbook.
Although the directive applies only to federal agencies, the message is clearly aimed at the broader market. Unsupported infrastructure isn’t a technical debt issue—it’s a risk exposure issue. If a device can’t be patched, monitored, and lifecycle-managed, it shouldn’t be on the network. In a threat landscape where initial access is everything, the perimeter is only as strong as the oldest box still sitting in the rack.

AI Vulnerability in ServiceNow Highlights Risks of AI Integration
A critical vulnerability uncovered in ServiceNow’s AI features demonstrated how deeply integrated AI can become both a utility and an attack vector. Researchers found that weak authentication and default credentials in legacy components — combined with powerful AI agents — allowed an attacker to impersonate users and gain administrative access, potentially pivoting across connected systems and data sources.
This flaw underscores a broader industry truth: as AI becomes woven into enterprise platforms, the boundary between traditional app security and AI security is collapsing. Attackers aren’t simply exploiting software bugs; they’re leveraging AI logic, APIs, and automation permissions to achieve lateral movement and privilege escalation. The vulnerability has since been patched, but the incident highlights the necessity of scoping AI agent capabilities strictly, tightening authentication controls, and continuously reviewing AI-enabled workflows for potential abuse.
For cloud security teams, this represents a cautionary example of how automation can inadvertently widen the attack surface when not governed with strict least-privilege and monitoring practices.

3. Substack Notifies Users After Hacker Claims 700K-Record Leak
Substack has started notifying customers about a newly disclosed security incident after a hacker claimed on the dark web to be sitting on a large cache of user records. In a notice signed by CEO Chris Best, the company said it found evidence on February 3, 2026 that an unauthorized party had accessed a limited set of user data—data that appears to trace back to October 2025.
Substack’s message draws a clear line around what was—and wasn’t—exposed. The company says passwords, payment card numbers, and other financial information were not accessed, but customer contact details and internal metadata were. That matters because even “non-financial” account data can be enough to fuel targeted phishing, SIM-swap attempts, and convincing account-takeover lures—especially when attackers can personalize messages with platform-specific context.
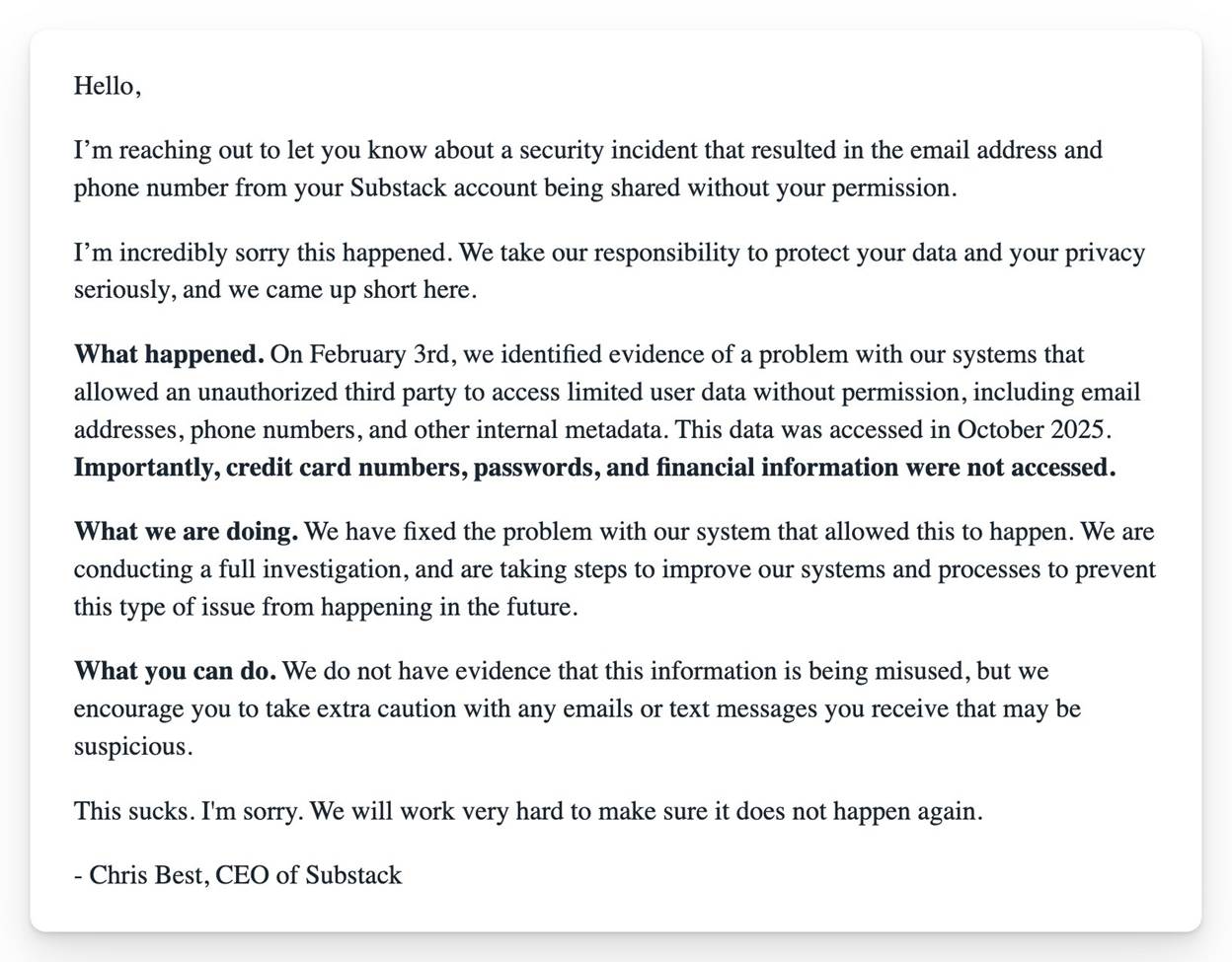
The hacker’s claim is louder than Substack’s confirmed scope: reports describe an alleged leak of nearly 700,000 records, potentially including names, emails, phone numbers, user IDs, Stripe IDs, profile details, and more. Substack has said it fixed the underlying issue and is investigating, but the public reporting makes clear that the precise size and completeness of the dataset being advertised is still uncertain.
For organizations and creators who rely on Substack as a distribution channel, the practical risk right now isn’t a drained credit card—it’s trust erosion and inbox exploitation. If you’re on the platform, treat unexpected “account support” emails and texts as hostile by default, avoid clicking through to login pages from messages, and enable stronger account protections wherever available. This is a reminder that breaches increasingly start with “basic” identity and contact data—and end with very real downstream compromises.
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about