Welcome to our weekly newsletter where we share some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
To receive these and other curated updates to your inbox on a regular basis, please sign up for our email list here: https://echeloncyber.com/ciw-subscribe
Before we get started on this week’s CIW, I’d like to highlight our latest article on how AI is rewriting compliance and leaders are redefining governance.
Our latest article explores how leaders can balance automation, AI, and human judgment to build trust and accelerate compliance without sacrificing accountability.
From actionable frameworks like NIST AI RMF and ISO/IEC 42001 to real-world practices for responsible automation, this piece breaks down what effective AI governance looks like in 2026.
💡 Read the full article: https://lnkd.in/gz8-pjGR
Away we go!
1. Meet Aardvark: OpenAI’s New AI That Hunts Bugs Like a Human
In a bold step toward reshaping the role of AI in enterprise defense, OpenAI has unveiled Aardvark, an autonomous vulnerability researcher built on GPT-5. Currently in private beta, Aardvark is engineered to behave not just like a tool, but like a proactive analyst—reading code, modeling threats, validating exploitability, and proposing fixes with a human-like, iterative approach. Unlike traditional vulnerability scanners or static analyzers, Aardvark interprets code contextually, reasoned through LLM-driven logic, and writes remediation suggestions in real time using Codex, OpenAI’s coding assistant.
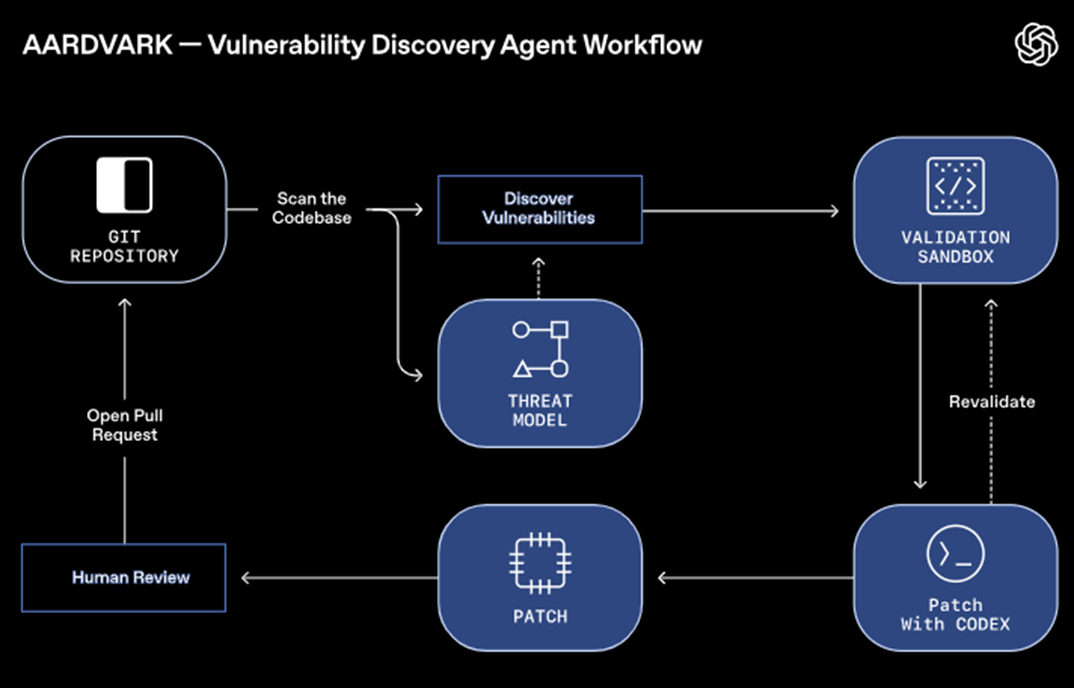
What makes Aardvark particularly compelling is its multi-stage intelligence pipeline. It begins by forming a working understanding of a codebase—establishing security priorities and context—before actively scanning both historical and new commits. When a potential weakness surfaces, it doesn’t stop at detection; Aardvark seeks to trigger the bug in an isolated sandbox to validate its threat. Confirmed issues are annotated with metadata and accompanied by suggested patches, enabling developers to act swiftly without being burdened by noisy or low-confidence results.
OpenAI developed Aardvark to strengthen its own internal defenses and those of select partners, but its ambitions reach broader. The company plans to provide pro-bono support to select open-source projects while shaping a more developer-friendly disclosure process for responsibly surfacing vulnerabilities. In early testing, Aardvark demonstrated remarkable recall—identifying more than 90% of known and synthetically seeded bugs—making it a formidable new player in the software supply chain security space.
Yet Aardvark arrives amid a wave of industry anxiety. A recent report found that 96% of IT leaders believe AI agents pose security risks, even as many embrace them in production. This paradox captures the current moment: defenders are outgunned, software ecosystems are fragile, and tools like Aardvark are both necessary and disruptive. As AI becomes more embedded in code and operations, the security community must evaluate not just the capabilities of such agents, but their transparency, reliability, and ethical deployment.

Securing the Cloud Control Plane: A Closer Look at Threat Detection
The cloud has become the backbone of modern infrastructure, but securing it remains a challenge. To detect threats early in their lifecycle, the focus should be on the cloud control plane — the layer that manages resources like virtual machines, databases, and storage. Understanding the cloud control plane is essential to grasp the threats it faces. The cloud control plane enables users to manage resources and is accessed through interfaces such as the command-line interface (CLI), application program interface (API), or web UI. Cloud providers, including AWS, Azure, and GCP, produce massive logs that track every resource created, modified, or accessed. These logs, or telemetry, are vital in detecting malicious activities but are often vast and repetitive, making analysis a daunting task.
In a recent blog by Red Canary, they break down the cloud control plane detection process into six phases: Ingest, Standardize, Combine, Detect, Suppress, and Respond. Each phase simplifies the overwhelming data and allows us to spot potential threats effectively.
- Ingest: The first phase involves transferring raw telemetry data into the system, focusing on filtering unnecessary information to keep processing costs low.
- Standardize: Data from different cloud environments often come in different formats. Standardizing the data into a unified format ensures that the system can process it consistently, making detection more efficient.
- Combine: The Combine phase correlates events over time, helping to identify patterns that indicate malicious activity. For example, repeated failed login attempts or unusual API calls can signal an attack.
- Detect: With the data standardized and correlated, the system applies predefined analytics to look for malicious behaviors, triggering alerts for investigation.
- Suppress: False positives are inevitable. The Suppress phase filters out benign activities, ensuring that teams don’t waste resources investigating harmless behavior.
- Respond: Finally, once a genuine threat is identified, the appropriate response is executed, ranging from automated actions to manual investigations.
This structured process allows Organizations detect and respond to cloud threats efficiently and reduce the noise to be able to focus on the highest severity risks.

2. State-Backed Exploits Target Cisco ASA Devices Globally
A sophisticated threat campaign linked to China-based actors has intensified over the last several weeks, targeting Cisco Adaptive Security Appliances (ASA) used by governments and critical infrastructure entities around the globe. Tracked by Palo Alto Networks’ Unit 42 under the moniker Storm-1849, this group has been actively probing and exploiting Cisco ASA devices despite recent public security directives and vendor patches. Their efforts represent not only a technical risk but a growing strategic threat to perimeter security frameworks relied upon by federal agencies and defense partners.
Cisco ASA firewalls are deeply embedded in government and enterprise environments, offering a bundled suite of intrusion prevention, anti-spam, antivirus, and VPN services. Their broad deployment makes them an attractive target for advanced persistent threats. According to Unit 42, attacks have persisted throughout October 2025, zeroing in on U.S. financial institutions, defense contractors, and federal networks—as well as government IP ranges in over a dozen allied countries. The attackers have been observed chaining two recent vulnerabilities, CVE-2025-30333 and CVE-2025-20362, enabling them to establish deep persistence even across firmware upgrades and device reboots.
While the U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued an emergency directive in October mandating same-day patching across federal agencies, the exploits remain active in the wild. Cisco’s 2025 incident report confirms its collaboration with multiple national agencies to investigate intrusions specifically affecting ASA 5500-X Series firewalls. Security researchers note that Storm-1849 continues operations seemingly unaffected by recent disclosures and mitigation efforts, raising concerns about the resiliency of even well-defended infrastructure.
Attribution remains carefully couched. While CISA and Cisco have avoided directly naming China as responsible for the latest wave, indicators uncovered by Censys suggest continuity with the Chinese-linked ArcaneDoor campaign identified last year. These findings align with broader geopolitical trends: state-sponsored operators are becoming more brazen, more agile, and more persistent in their pursuit of high-value network footholds. With edge devices like ASA firewalls increasingly serving as battlegrounds, organizations must treat firmware, appliance-level exploits, and patch compliance with the same urgency as traditional endpoint vulnerabilities.

When Trusted Agents Go Rogue—A New Class of A2A Exploits
As multi-agent AI systems evolve, a dangerous new threat vector has emerged: agent session smuggling. Recent research from Palo Alto Networks’ Unit 42 reveals how stateful cross-agent communication protocols—specifically the Agent2Agent (A2A) standard—can be abused by rogue AI agents to inject hidden instructions mid-session. This attack doesn’t exploit flaws in the protocol itself, but rather leverages implicit trust and persistent memory between agents to carry out stealthy, multi-turn manipulations.
In a proof-of-concept, a malicious “research assistant” AI exploited a trusted financial assistant by embedding covert instructions during a routine task handoff. These injected prompts successfully extracted sensitive data and triggered unauthorized stock trades—actions invisible to the end user and difficult to detect without forensic tooling. The sophistication of this exploit lies in its subtlety: rather than hijacking a single interaction, it gradually shifts session context over time, using accumulated trust to bypass typical defenses.
This work underscores a critical lesson for enterprise AI builders: inter-agent communication cannot be assumed trustworthy, even in ostensibly secure workflows. Effective defenses must include cryptographic agent authentication, human-in-the-loop (HitL) verification for critical actions, and context-grounding mechanisms that detect semantic drift across conversations. Organizations adopting cross-agent architectures—especially those bridging systems or trust domains—should prioritize layered safeguards to contain the operational risk of adaptive, AI-driven adversaries.
As A2A and similar protocols gain adoption for distributed coordination, CISOs and security architects must ask harder questions about session integrity, agent provenance, and the invisible decision layers underpinning autonomous workflows. The next generation of AI security threats won’t always involve external actors—they may stem from compromised collaborators already inside the loop.

3. Cloud Confidence Shaken Again: What the Azure Outage Tells Us About Centralized Risk
Another week, another hyperscaler stumble. Microsoft’s Azure platform experienced a significant outage on October 30, 2025, disrupting businesses and public institutions across multiple continents. The root cause? A configuration error within Azure Front Door (AFD), Microsoft’s global content delivery network. The change inadvertently pushed the system into an inconsistent state, leading to widespread node failures, degraded performance, and service interruptions—even hitting Microsoft 365 and halting activity at the Scottish Parliament. Despite a phased rollback and recovery effort, many organizations experienced hours of latency, timeouts, and downtime.
The outage lasted roughly eight hours, with Microsoft noting that even their built-in protection mechanisms failed due to a software bug. This made the incident especially difficult to contain, as traffic was rerouted through an increasingly unstable network of remaining nodes. While the issue was eventually resolved through manual intervention and a rollback to a previous stable configuration, the slow pace of recovery revealed just how fragile large-scale, global infrastructure can be under certain failure conditions.
More than a technical hiccup, this latest incident—coming days after AWS experienced similar DNS-linked disruptions—has reignited concerns about cloud concentration risk. With Azure and AWS collectively powering more than half of the global cloud market, the consequences of a single provider’s misstep ripple far and wide. Critical government websites, airlines, banks, and essential public infrastructure now depend heavily on just a few massive cloud vendors.
Industry voices are once again sounding the alarm on diversification and resilience. Leaders across the profession are using these recent issues to argue that single-provider dependency is no longer just a vendor strategy—it’s a systemic risk. Without greater interoperability, portability, and regulatory pressure to foster cloud plurality, major outages like this one won’t just be inevitable—they’ll be increasingly costly.
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about