Welcome to our weekly newsletter where we share some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
To receive these and other curated updates to your inbox on a regular basis, please sign up for our email list here: https://echeloncyber.com/ciw-subscribe
Also, we are always looking for great people to join our team. If you know anyone who fits the profiles for any of our open positions, drop me a line and let me know!
Before we get started on this week’s CIW, I’d like to honor all of the men and women that lost their lives in the tragedy of 9/11. Unlike most days, I will never forget exactly where I was when I heard the news of what was happening on that fateful day. The terrorists that targeted our way of life that day thought that they would destroy our country, they couldn’t have been more wrong. The United States is strong and resilient, and this tragedy unified the country in a way that could never be imagined. We must never forget the victims who lost their lives as well as the heroes attempting to save them.

1. Security Officials Concerns Raised Over Liability for Attacks
A trial began last Wednesday in San Francisco, where Joseph Sullivan, former Uber Chief Security Officer will face federal wire fraud charges. At the time of the breach, many criticized Uber of hiding the details of the breach and citing the bug bounty program as a way to treat the breach as a white-hat hack rather than nefarious data ransom.

Per a Justice Department press release, “Rather than report the 2016 breach, Sullivan allegedly took deliberate steps to prevent knowledge of the breach from reaching the FTC. For example, as described above, Sullivan arranged to pay off the hackers in exchange for them signing non-disclosure agreements that contained the false representation that the hackers did not take or store any data. In addition, Sullivan sought to pay the hackers off by funneling the payoff through a bug bounty program—a program in which a third-party intermediary arranges payment to so-called “white hat” hackers who point out security issues but have not actually compromised data.”
Typically, when personal non-public information is exposed in such a way, it is a reported data breach and organization’s must go public with the news. However, in this case, attorney’s advised Mr. Sullivan that the matter could be treated as a bug bounty and wasn’t a reportable breach if so. Uber made the hackers sign a non-disclosure agreement and ultimately paid the hackers $100,000. This case will have major implications on the legal process for reporting a breach and it will be very interesting to see how it plays out.
2. GIFShell Attack Creates Reverse Shell Using Microsoft Teams GIFs
A recent Bleeping Computer article explains a novel way to social engineer Teams users and then exploit Teams to be able to create a reverse shell within the target environment. Security researcher Bobby Rauch shows how Microsoft Teams may allow a threat actor to send malicious files to a Teams user, whether in their own tenant or not, and allows the threat actor to spoof it to look like a harmless image. However, when the user clicks it, it will actually download a file from wherever the threat actor is pointing it.
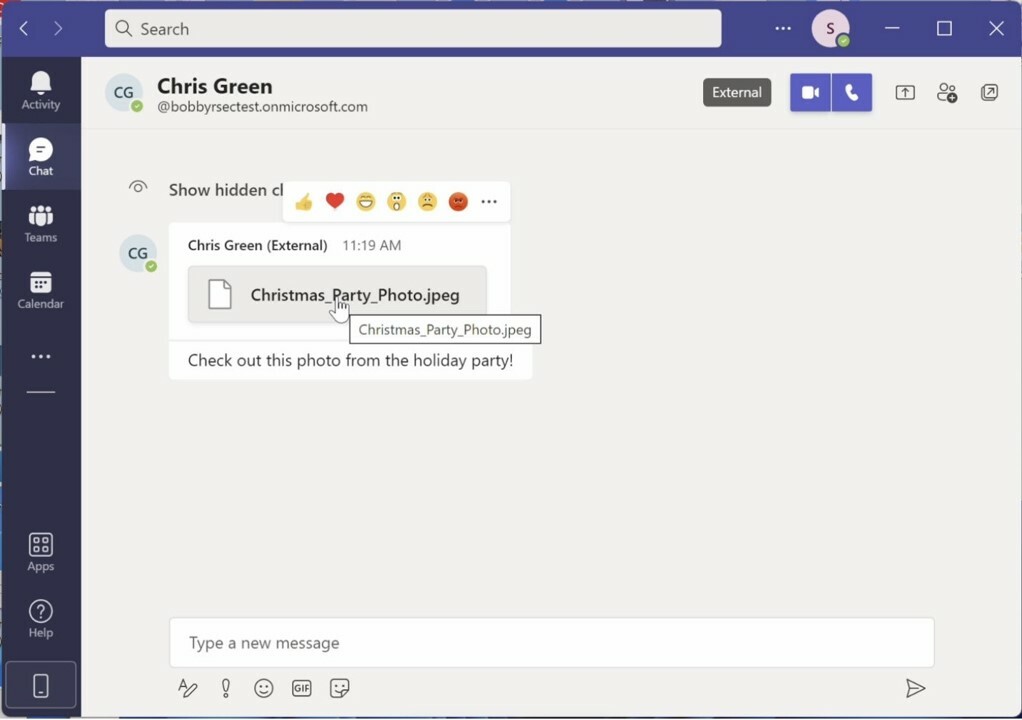
Source: Bobby Rauch
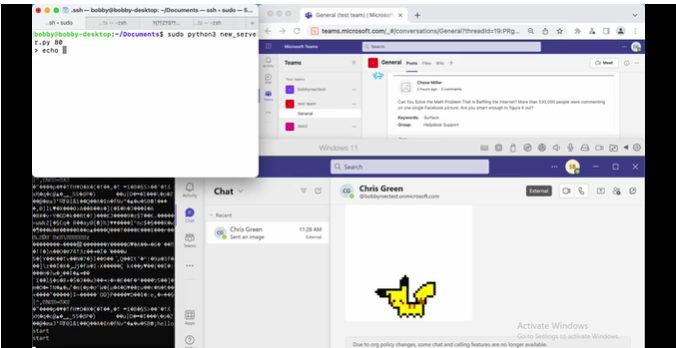
In this attack, in which Bobby Rauch describes as ‘GIFShell,’ an attacker can create a reverse shell that delivers malicious code through base64 encoded GIFs in Microsoft Teams. Output from this shell can then be exfiltrated through GIFs retrieved through Microsoft’s own infrastructure. Rauch calls out several insecure design elements and vulnerabilities that allow for this attack to occur, issues like default settings in Teams allowing for external domains to communicate, Teams messages stored in plain text, etc. Full details on this attack and how it can be executed can be found on Rauch’s blog. Microsoft has acknowledged these issues at this time, however they noted in a response to the research that, “do not meet the bar for an urgent security fix.” Always be careful with those GIFs people!
3. New Google Chrome Zero-Day Has Users Scrambling to Update
Google recently released a Chrome update to fix a new zero-day flaw. This was classified as a high rated vulnerability, CVE-2022-3075: Insufficient data validation in Mojo. Mojo is a collection of runtime libraries that provide a platform-agnostic mechanism for inter-process communication. An attacker can exploit this vulnerability by persuading a victim to visit a specially crafted website, to bypass security restrictions.

Google has also reported that it is aware of reports of this vulnerability being exploited in the wild. Google Chrome users on Windows, Mac and Linux platforms are advised to install the latest security updates immediately. Users are also being encouraged to enable the automatic update function in Chrome to ensure that the software is updated automatically. Users of other Chromium-based browsers such as Microsoft Edge, Brave, Opera, and Vivaldi are also advised to apply the fixes as and when they become available.
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about