Welcome to our weekly newsletter where we share some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
To receive these and other curated updates to your inbox on a regular basis, please sign up for our email list here: https://echeloncyber.com/ciw-subscribe
Also, we are always looking for great people to join our team. If you know anyone who fits the profiles for any of our open positions, drop me a line and let us know!
Before we get started on this week’s CIW, I’d like to highlight the recent news that Echelon is a strategic services partner of CrowdStrike, the global cybersecurity leader with an advanced cloud-native platform for protecting endpoints, cloud workloads, identities and data. We offer our suite of strategic proactive cybersecurity services alongside the CrowdStrike professional services team and couldn’t be more proud of the hard work of our professionals!
Away we go!
1. LastPass Announces Another Security Incident
In a recent blog post from LastPass, they announced that they “…recently detected unusual activity within a third-party cloud storage service, which is currently shared by both LastPass and its affiliate, GoTo. We immediately launched an investigation, engaged Mandiant, a leading security firm, and alerted law enforcement.” LastPass also noted in their blog post that certain elements of customer information were accessed; however, they remain confident that no customer secrets were accessed due to their “Zero Knowledge” architecture. LastPass did not explain what those “certain elements” were.
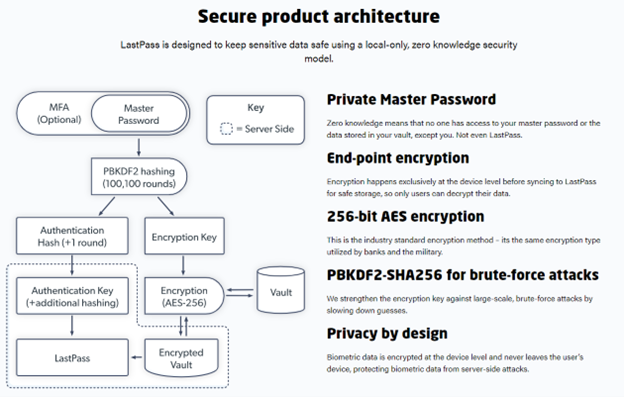
This would be the second time this year that LastPass has suffered a security incident of significant scale. Luckily, their encryption methodology has saved them from a major customer data breach of customer secrets. Back in August of this year, attackers were able to access LastPass source code while they compromised a developer account for several days. This story will be interesting to watch as the investigation is on-going, hopefully there are no other major revelations, and this is the last we hear of it.
2. Huge Trove of Phone Numbers (360 Million) for Sale on Dark Web
There have been several reports in the past week that have postulated that a huge leak of phone number data on the dark web belonged to WhatsApp. Check Point Research (CPR) recently released a detailed blog post analyzing the data, which they said included 360 million phone numbers from 108 countries in total.
When the data went up for sale on BreachForums in November, the hacker selling the information stated that the data was from WhatsApp, and contained personal information of 487 million WhatsApp users from 84 countries. The full list went on sale for several days and is now being distributed freely on the dark web.

The CheckPoint researchers could not confirm that the source of the stolen data was from WhatsApp. In fact, the research cited some other research that tied the stolen data back to a 2019 Facebook data breach. This is a good reminder of just how much stolen data is floating around out there that can be used to carry out other types of attacks against unwitting users.
3. Krebs Notes That ConnectWise Quietly Patches Flaw That Helps Phishers
A recent report from Brian Krebs calls out some excellent research from Ken Pyle about how the popular ConnectWise remote management tool could be used by attackers to facilitate their operations. ConnectWise is a populate remote management tool that is used by countless MSP and other IT services providers. These flaws uncovered by Pyle also appear to be currently used in the wild by threat actors, as evidenced by this ConnectWise blog posting.
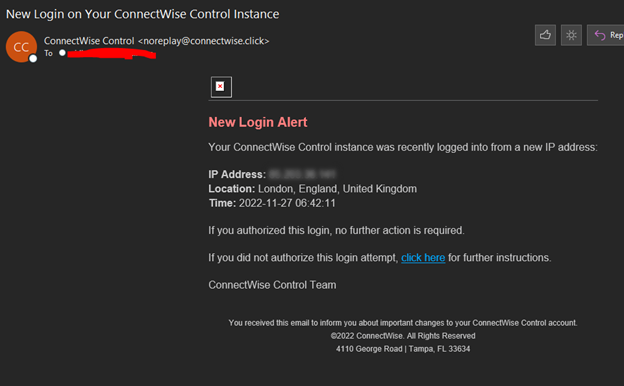
Image: KrebsonSecurity.com
The major issue at hand is that the ConnectWise client executable (the thing downloaded by the person receiving remote support) gets generated based on -client controlled parameters. Meaning, an attacker can create a ConnectWise account with little validation, create an executable that uses the ConnectWise infrastructure to point them to their evil servers. This is especially bad because the ConnectWise executable looks legitimate and is even signed by the company.
ConnectWise pushed out an update a few weeks ago to address this issue, version 22.9.10032. As noted by Ken Pyle, he mentioned that the release notes provided only a fairly vague description of the issue, “Add additional validation of client installer URL parameters to inhibit certain social engineering attacks.”
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about