Welcome to our weekly post where I will be sharing some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
You can also Subscribe to receive Cyber Intelligence Weekly in your inbox each week.
Before we get started on this week’s CIW, I’d like to highlight a new article from Senior Cybersecurity Consultant, James Stahl. In this article, Continuous Penetration Testing: Shattering the Hourglass” he talks about the concepts or regular penetration testing through a continuous and semi-autonomous model. This type of paradigm shift changes penetration testing from a one-time exercise intended to find vulnerabilities to a regular exercise that can find vulnerabilities but also confirm controls on a regular basis. Please check it out here!

Away we go!
1. Chinese Surveillance Key Area of Concern as 2022 Olympics Kickoff
As the 2022 Olympics in Beijing kickoff, athletes from all over the world will be attending the game with varied guidance from their home countries on how to handle the potential Chinese surveillance they will be under. As China has established a culture of mass surveillance, many are concerned about the privacy of athletes and other visitors during the 2022 games.
A report from the U.S. Olympic & Paralympic Committee obtained by Axios states that, "No guarantees of data privacy or security should be made regardless of the security technology utilized. Assume that every device and every communication, transaction, and online activity will be monitored.” Many countries are instructing their athletes and potential visitors that they should consider burner phones and other devices while traveling and to carefully protect their communications.
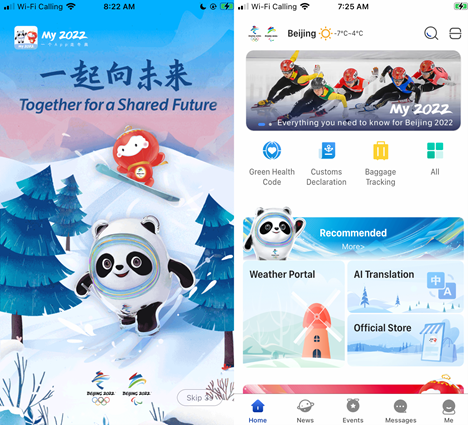
This news all comes to light not long after Citizen Lab reported that the MY2022 app, a mobile application for Olympic visitors, has some serious data protection flaws in it. Keep in mind that this app is being required of all attendees to download as well as report their health data on a daily basis to monitor for COVID19.
The explosion of hyper interconnectivity mixed with mobile devices for everything and everyone in a surveillance focused state have made this year’s Olympics a potential privacy disaster.
2. Major German Oil Storage Company Hit by BlackCat Ransomware
Oiltanking Group out of Germany has succumbed to a ransomware attack that is highly reminiscent of the Colonial Pipeline attack of last year. Per multiple reports, the IT systems of Oiltanking Group have been shut down. The ransomware strain that was utilized is a highly popular new strain of ransomware called BlackCat. The ransomware is unique and novel, given the coding language that is has been written in (Rust).

In a stunning interview with an analyst from Recorded Future, a member of the BlackCat ransomware gang opens up about their plans, motivations and other interesting topics. Here is a quote from the article about why they used the Rust programming language:
DS: Why RUST? Are you trying to obfuscate previously used code? Cross-compiling?
ALPHV: RUST is chosen as a modern cross-platform low-level programming language. In the console command, the project name is alphv-N(ext)G(eneration). We have made a truly new product, with a new look and approach that meets modern requirements for both a RaaS solution and high-class commercial software.
Oiltanking Group owns and operates 11 terminals in Germany with a total storage capacity of 2.375 million cubic meters of fuel. What is also interesting is how reliant Germany is on Russian oil and gas and how this comes at a time of great tension with potential war looming on the eastern front amid heightened tensions in the region.
The threat actors behind the new BlackCat ransomware and this attack are being linked to the Darkside ransomware threat actors, who carried out the Colonial Pipeline attack, according to a new report from Bloomberg. It has been reported that this group has been very active since December and that they are targeting a wide range of industries, from construction and retail to insurance and professional services. This is yet another example of just how threat actors constantly evolve and how we must evolve with them.
3. Man at Home in Pajamas, Takes Down North Korean Internet
One of the most interesting stories from last week was the story from Wired that describes a security analyst and threat researcher, “P4x”, who supposedly single handedly took down much of the North Korean internet for several days from the comforts of his own home. I won’t try to summarize this one too much, because the story itself is a must read, but essentially P4x decided to “hack back” after being targeted by North Korea with malware. He reportedly reported it to US authorities, but after a year or more nothing was done and clearly saw that there would be no consequences. He apparently wanted to prove a point, and so it seems he did! Always fascinating stuff by the Wired reporters.