Welcome to our weekly newsletter where we share some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
To receive these and other curated updates to your inbox on a regular basis, please sign up for our email list here: https://echeloncyber.com/ciw-subscribe
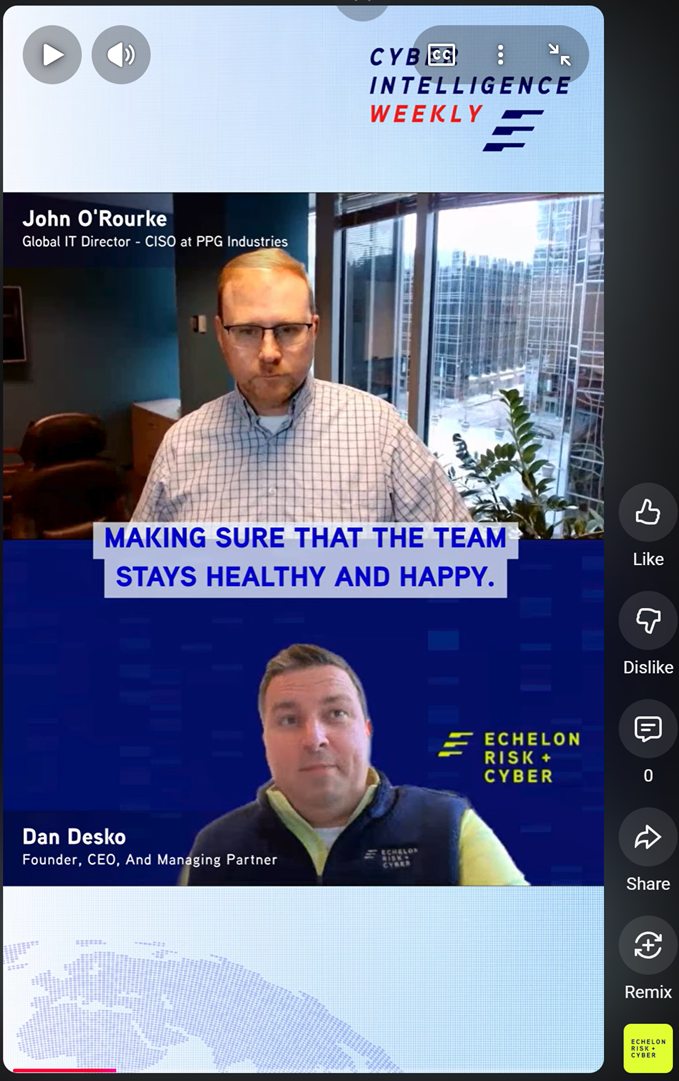
Before we turn to this week’s edition of Cyber Intelligence Weekly, I want to introduce a new CISO Spotlight Series: The Human Side of Cybersecurity.
This series is grounded in conversation rather than commentary. It centers on CISOs who are in the seat—navigating real leadership pressure, complex risk decisions, and the human realities of building and sustaining security programs. Some are earlier in their journey, others further along paths many of you may recognize or aspire toward. What they share isn’t theory. It’s experience—earned through moments of progress, frustration, growth, and reflection. These conversations are for the professionals who show up every day to quietly carry the weight of this industry.
Check out this short clip with John O'Rourke, CISO at PPG Industries, where we talk about how security burnout isn’t a people problem — it’s a system problem.
This quick clip highlights practical ways high-performing security teams stay resilient: rotating responsibilities, cross-training to reduce single points of failure, encouraging efficient and truly unplugged PTO, and building a culture grounded in trust. The takeaway is simple but powerful — sustainable security programs are built on teams that have the space to recover, grow, and support each other. Strong defenses start with a healthy team.
Clip: https://youtube.com/shorts/xAbUkNv882M?si=0nym142eFbaH51HA
Full Interview: https://youtu.be/vgI7VRcITI4?si=XBtyL9TAW8iPstfW
____________________________________
RSA 2026, Come Meet With Us!
Also, to highlight upcoming events, we hope to meet you at RSAC 2026! If you are heading out to RSA and want to meet up with the Echelon team, come see us at our exclusive happy hour at the prestigious Olympic Club, a quiet oasis from the busy hustle and bustle of RSA.
Join Echelon Risk + Cyber for our annual RSA Happy Hour at The Olympic Club on Monday, March 23, from 3:00–5:00 PM PT, just before the official RSA Welcome Reception, with our sponsors Drata and Schellman!
Good people, great conversations, easy networking, no pressure.
📍 The Olympic Club, San Francisco
👉 Reserve your spot here: https://lnkd.in/enj3Q9D3

Away we go!
1. Phishing’s Next Evolution: How “Starkiller” Turns MFA Into a False Sense of Security
Security researchers are warning about a new phishing-as-a-service platform that reflects how quickly cybercrime is adopting enterprise-grade capabilities. Known as Starkiller, the service doesn’t rely on fake login pages. Instead, it loads the real website the victim expects to see and silently acts as a proxy between the user and the legitimate service—capturing credentials, session data, and authentication tokens in real time.
The technique changes the game. When a victim clicks a deceptive link, Starkiller spins up infrastructure that relays every interaction to the actual site while logging everything the user enters. Because the authentication process happens against the legitimate platform, even multi-factor authentication works as designed—yet the attacker still walks away with the active session. In practice, this allows criminals to bypass MFA without breaking it.
The service is designed for scale and ease of use. Operators can choose brands like Microsoft, Google, or Apple, generate convincing URLs that mimic trusted domains, and launch campaigns without managing infrastructure themselves. Behind the scenes, Starkiller captures keystrokes, session cookies, location data, and account details, while sending real-time alerts when credentials are harvested. It even provides performance dashboards and campaign analytics—features that look more like a legitimate SaaS platform than a traditional phishing kit.
The bigger concern is what this represents. Tools like Starkiller lower the technical barrier for attackers while undermining traditional defenses such as domain blocklists and static page detection. As phishing infrastructure becomes more automated, interactive, and commercially packaged, organizations can no longer rely on MFA alone as a safety net. The control environment has to evolve toward phishing-resistant authentication, stronger session protections, and a security strategy that assumes the attacker may already be inside the login flow.

Cloud Security Threatened by a Growing “Complexity Gap”
Cloud environments continue to expand at a pace far exceeding many security teams’ ability to defend them effectively, driven in part by rapid adoption of AI and automation. According to recent analysis, this widening “complexity gap” means traditional, manually driven cloud defenses are increasingly mismatched against adversaries using AI-enabled tooling that can scale attacks at machine speed. The result is a systemic risk where defenders struggle to keep up with attack costs that approach zero due to automation advantages. As cloud footprint and services sprawl, cloud security must transition from reactive blocking to AI-driven, real-time, preemptive defense models that impose uncertainty on attackers and reduce attack efficacy.
This trend reflects a broader industry challenge identified in cloud security research: expanding attack surfaces from multi-cloud, hybrid environments, and AI services create fragmented visibility and inconsistent protection. Mismanaged identities, insecure APIs, and tool sprawl exacerbate risk, requiring modern cloud security strategies that unify posture, detection, and response rather than relying on siloed tooling.
For CISOs and security leaders, the key takeaway is that cloud security cannot simply scale by adding defensive tools. Instead, teams need automation, integrated threat intelligence, and contextual risk prioritization to outpace threats. This includes aligning security controls with business risk, consolidating cloud security workflows, and investing in AI-capable detection engines that can operate at or above attacker speed.

2. Nation-State Hackers Exploit Critical Dell Disaster Recovery Flaw
A critical vulnerability in a widely used Dell disaster recovery platform is drawing urgent attention from federal authorities after evidence of active exploitation by a Chinese state-linked threat group. The flaw, tracked as CVE-2026-22769, carries a maximum severity rating and affects RecoverPoint for Virtual Machines, a tool many organizations rely on to replicate systems and restore operations after outages or cyber incidents. The Cybersecurity and Infrastructure Security Agency (CISA) confirmed exploitation and ordered U.S. federal agencies to apply patches within days—an unusually tight deadline that underscores the seriousness of the threat.
At the center of the issue is a hard-coded credential embedded in the product. Once discovered, the weakness allows an unauthenticated attacker to gain deep access, potentially reaching root-level control. Security researchers from Google and Mandiant linked the activity to a long-running campaign associated with a Chinese espionage cluster tied to Silk Typhoon. During intrusions, the actors deployed updated versions of their BRICKSTORM backdoor and a newer tool, GRIMBOLT, designed to maintain persistence while minimizing forensic traces.
The target selection is strategic. Disaster recovery and replication platforms operate with elevated privileges and sit at the heart of an organization’s resilience architecture. Compromising this layer gives attackers more than system access—it provides visibility into infrastructure design, replicated data, and the ability to influence what gets restored during a crisis. Researchers note that these specialized appliances often lack traditional endpoint detection capabilities, allowing threat actors to remain undetected for extended periods.
The broader lesson is one security leaders have seen repeatedly: attackers are moving toward high-leverage infrastructure that quietly controls recovery, identity, and core operations. When resilience platforms become the entry point, the impact extends beyond data theft to operational control. Organizations running affected versions should treat this as an immediate priority—not just patching the vulnerability, but reviewing access controls, monitoring privileged infrastructure, and validating that the systems designed to restore operations haven’t quietly become part of the attack path.

Coding Agents: The Insider Threat You Installed Yourself
An emerging security analysis warns that AI coding agents—initially adopted for productivity gains—can inadvertently become insider threats if deployed without adequate visibility and control. These agents, such as Claude Code or GitHub-style assistants, are no longer passive suggestion tools; they execute code, run commands, and interact with local systems autonomously, often with broad access rights. Without strict oversight, they blur the boundary between trusted tooling and an internal threat actor that can modify files, invoke external tools, or interact with APIs without clear audit trails.
The core issue is visibility deficiency: organizations rarely know precisely what an AI coding agent touched, what external resources it queried, or what side-effects its generated code may introduce into production pipelines. This blind trust creates a form of cyber insider threat—distinct from traditional human insiders—where the agent’s actions can create insecure configurations, inadvertently expose secrets, or introduce exploitable code paths.
Security practitioners are already framing this problem in familiar threat models. Modern research shows that autonomous coding agents can harbor systemic security flaws, with analyses demonstrating how insufficiently constrained AI workflows yield execution of arbitrary commands or data exfiltration without user interaction or review.
To mitigate this emerging risk, organizations must treat AI coding agents like any powerful internal automation: enforce strict sandboxing, implement comprehensive logging and audit controls, enforce least privilege, and ensure generated outputs pass the same security validation pipelines as human-written code. Additionally, adopting prompt hygiene monitoring and model interaction governance can help defenders identify adversarial prompt patterns or tainted model behaviors before they impact environments.

3. Living With the Threat: Volt Typhoon Still Embedded in U.S. Infrastructure
The warnings about Volt Typhoon have grown more sobering. According to a new industry analysis, the Chinese state-linked group is still actively embedded inside U.S. critical infrastructure—and in some cases, the intrusions may never be discovered. After nearly three years of coordinated government and industry efforts to evict the threat actor from water, power, and other essential services, operational technology security firm Dragos says the reality is uncomfortable: portions of U.S. infrastructure are likely already compromised and may remain that way for years.
Volt Typhoon’s strategy isn’t about quick disruption. It’s about quiet persistence. The group has continued targeting utilities through 2025, focusing on gaining long-term access and mapping operational environments across the United States and allied nations. U.S. officials believe the objective is strategic pre-positioning—establishing footholds inside operational technology networks that could be activated during a geopolitical crisis to slow military mobilization or disrupt critical services at scale.
What makes the threat particularly difficult to eradicate is the uneven security maturity across sectors. Large electric utilities increasingly have the visibility and capability to detect sophisticated intrusions. Smaller and resource-constrained organizations—especially in the water and municipal sectors—often do not. According to Dragos leadership, while it may be technically possible to hunt for these compromises everywhere, many organizations will never reach the level of monitoring and expertise required to find them. The result is a growing acceptance across the security community that some adversary access may persist undetected.
The report also highlights a supporting actor known as SYLVANITE, an initial access group that targets operational environments and hands those footholds to Volt Typhoon for long-term operations. Recent campaigns exploiting widely used enterprise and infrastructure tools have given attackers visibility into GIS data, sensor information, and operational processes—intelligence that could enable highly targeted disruption in the future. The shift is clear: this is no longer just about stealing data from IT networks. Nation-state actors are learning the physical environment, the operational dependencies, and the real-world impact pathways inside critical infrastructure.
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about