Welcome to our weekly newsletter where we share some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
To receive these and other curated updates to your inbox on a regular basis, please sign up for our email list here: https://echeloncyber.com/ciw-subscribe
Before we get started on this week’s CIW, I’d like to highlight that Echelon Risk + Cyber is proud to be represented by Dan Desko (me!), Launa Rich, and Chris Furtick at RSA this WEEK!
Join Dan, Launa, and Chris at RSA! They are ready to dive into discussions on the latest cyber defense techniques, exchange key insights, or help you enhance your network with their seasoned expertise.
For more details on how you can interact with us at RSA, check out our page: https://lnkd.in/dW8hvcNy
We’re excited to turn #RSAC into a focal point for partnership and creativity. See you there!
Solution Partner Highlight – runZero’s CAASM Platform

Echelon Risk + Cyber proudly cultivates a diverse network of strategic relationships with leading vendors in the cybersecurity industry. These collaborations empower Echelon to deliver premium services to our clients through cutting-edge technology and valuable insights. In our ongoing effort to bring top-shelf knowledge, each week, we want to spotlight a distinguished partner solution offered at Echelon. This week’s focus is on runZero’s CAASM Platform.
runZero’s Cyber Asset Attack Surface Management (CAASM) Platform offers swift visibility over your organization, providing comprehensive insights within minutes. This platform grants unparalleled oversight across IT, OT, IoT, cloud, and mobile domains, uncovering risky, unknown, and unmanaged assets. The runZero Platform seamlessly integrates powerful proprietary active scanning, native passive discovery, and API integrations to reveal exposures rapidly. No agents, credentials, or hardware are necessary.
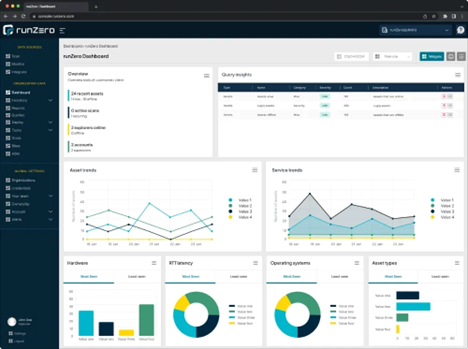
Key features of the runZero platform include:
- Attack Surface Analysis: Gain comprehensive insights into your attack surfaces.
- Network Insights: Visualize network topology and segmentation accurately.
- Unknown Subnets: Safely uncover hidden and risky subnets.
- OT Support: Safely discover fragile OT devices with purpose-built capabilities.
- Data Unification: Aggregate, correlate, and de-dupe data from multiple sources seamlessly.
- Seamless Integration: Ensure accuracy in CMDB and SIEM with seamless integrations.
With the conclusion of the insight into runZero’s Platform, we look ahead with anticipation. Echelon Risk + Cyber remains dedicated to pushing the boundaries of cybersecurity innovation, forging partnerships that empower us to stay at the forefront of industry trends. If your organization is grappling with specific security challenges, allow Echelon to help alleviate the burden. Reach out to discuss how we might help your organization and stay tuned for more solution highlights in the weeks to come!
Away we go!
1. Biden's Bold Blueprint to Shield Critical Infrastructure from Cyber Threats
In a bid to further fortify the United States against a spectrum of threats ranging from cyber assaults to climate-related disasters, President Joe Biden has unveiled a comprehensive overhaul of the nation's strategy for safeguarding critical infrastructure. Signed into effect on Tuesday, the national security memorandum supersedes a 2013 directive, delineating a collaborative framework among federal agencies, private enterprises, and local governments to bolster the security of pivotal sectors like healthcare, energy, and transportation. With an evolving landscape fraught with perils such as foreign cyber intrusions, domestic extremist activities, and escalating climate-induced calamities, the updated directive assumes paramount importance in mitigating vulnerabilities inherent in essential services.
The memorandum articulates three primary objectives: formalizing the Department of Homeland Security's Cybersecurity and Infrastructure Security Agency (CISA) as the principal guardian against adversarial actions and natural hazards, enhancing public-private partnerships through accelerated information exchange, and establishing minimum cybersecurity standards for sectors lacking regulatory frameworks. This regulatory paradigm shift signifies a departure from prior reliance on voluntary cooperation towards a more proactive stance, evidenced by recent cyber regulations imposed on key industries like aviation and healthcare. Moreover, the directive underscores the imperative of cohesive intelligence-sharing mechanisms between government entities and private entities to proactively counter emerging threats.
As the government recalibrates its defensive apparatus, the memorandum accentuates the pivotal role of CISA, elevating its authority as a linchpin in orchestrating infrastructure security initiatives. CISA's mandate encompasses orchestrating risk assessments, furnishing guidance to agencies, and identifying systemically crucial entities crucial to national resilience. While the memorandum preserves the existing sector-based infrastructure framework, it remains agile to accommodate evolving risks, as underscored by provisions for biennial risk management evaluations. Emblematic of a proactive stance towards safeguarding national interests, the memorandum epitomizes a pivotal stride towards fortifying the nation's resilience amid an increasingly perilous landscape.
2. FCC Fines Major U.S. Wireless Carriers for Selling Customer Location Data
The Federal Communications Commission (FCC) has imposed fines totaling nearly $200 million on the four major U.S. wireless carriers — AT&T, Sprint, T-Mobile, and Verizon. This penalty follows a four-year investigation into the carriers' unauthorized sharing of customer location data without obtaining consent. The FCC found that the companies sold access to customers' location information to data aggregators, who then resold it to third-party service providers.
The FCC revealed that each carrier attempted to delegate its responsibility of obtaining customer consent to downstream data recipients. However, this often resulted in no valid consent being obtained. The carriers continued sharing customer data even after becoming aware of the lack of safeguards, failing to protect it from unauthorized access. The investigation also indicated that AT&T had provided access to customer data to at least 88 third parties, Verizon to 67, Sprint to 86, and T-Mobile to 75.
The investigation was triggered by Sen. Ron Wyden (D-Ore.), who exposed how companies like Securus Technologies had been selling location data from major carriers to law enforcement. Further scrutiny revealed that LocationSmart, a data aggregator working with these carriers, had a public demo online that could be exploited to track any mobile phone in North America. Although the carriers pledged to cease data sharing agreements with third parties, reports in 2019 showed that little had changed.
Despite the significant fines imposed on these carriers, they represent only a fraction of each carrier’s annual revenue, with Verizon’s $47 million fine being less than 1% of its 2023 wireless revenue. The fine amounts were determined based on the number of days carriers continued sharing location data after being notified of the illegality, with AT&T and Verizon taking over 320 days to halt their data sharing agreements, while Sprint took 386 days and T-Mobile 275 days.
3. Massive Data Breach at Outabox Sparks Debate Over Biometric Privacy
Outabox, an Australian firm providing facial recognition technology to bars and clubs, recently suffered a significant data breach that has triggered alarm over the security of biometric data. The compromised information includes personal data collected through Outabox's kiosks, which were designed to scan visitors’ faces and measure their temperatures in response to the COVID-19 pandemic. Additionally, the kiosks were used to monitor problem gamblers participating in a self-exclusion initiative.
The incident was exposed by a website named "Have I Been Outaboxed," which claims to have over a million records from Outabox’s databases, including sensitive biometric data, driving licenses, and club membership information. The website, allegedly run by former Outabox developers, details the lax internal controls that led to the breach, revealing that the data was shared in an unsecured spreadsheet. It also implicates Outabox in exporting entire membership data of a gambling machine supplier, though the latter denies this claim.
The breach has drawn criticism from privacy advocates who have long raised concerns about facial recognition technology’s pervasive use in public spaces. They argue that the breach highlights the risks of entrusting sensitive biometric data to companies, urging for more stringent privacy laws and restrictions on such technology. The New South Wales police force has launched an investigation into the breach and made an arrest, but details remain scarce due to the ongoing investigation.
Outabox has dismissed the claims made on the "Have I Been Outaboxed" website as malicious and false, though cybersecurity experts remain cautious, warning that the biometric data breach could have serious implications. The incident underscores the growing need for robust data privacy laws to regulate the use of facial recognition systems, preventing such data from being exploited or mishandled.
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about