Welcome to our weekly post where I will be sharing some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
You can also Subscribe to receive Cyber Intelligence Weekly in your inbox each week.
Before we get started on this week’s CIW, I’d like to take a moment to remember Dr. Martin Luther King Jr. Dr. King was, and continues to be, an inspiration as he helped breakthrough barriers of racial inequality. Part of our core values at Echelon is that of Inclusivity & Diversity. This was not by accident. Personally, and professionally, I believe what Dr. King stood for should be celebrated and honored.
If you’d like to take a stroll through Dr. King’s life, this special edition of Google Earth, Remembering Martin Luther King Jr., is pretty great.

Away we go!
1. Russia Pretends to Care About Criminal Cybersecurity Activity for a Day
In a story that comes to as close to the age old, “Pigs Flying” fable, it was recently reported that the Russian Government has arrested members of the notorious REvil ransomware gang. The security service of the Russian Government, the FSB, announced the arrests in an online press release. The Russian News Agency, or (TASS), posted a video to YouTube of the supposed takedown. The clips show a forced entry into a home/apartment with agents making arrests and confiscating large amounts of cash and computer equipment. It should be noted that TASS is a state run news agency.
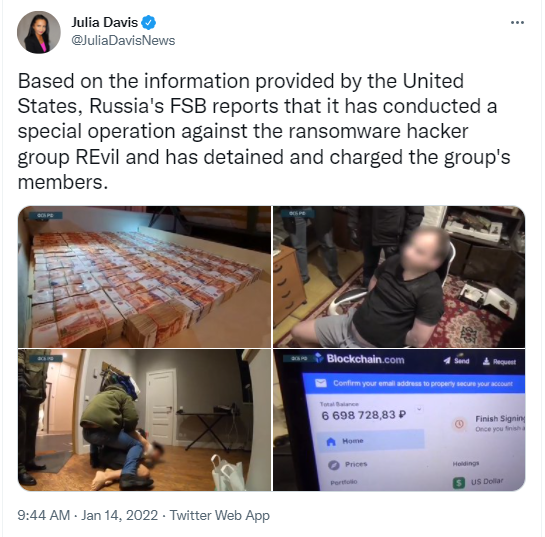
If you recall, REvil had been fingered lately for major ransomware attacks around the country against businesses and critical infrastructure. They also reportedly have enabled countless other hackers through the marketing and sale of their ransomware toolsets. Reports have claimed that the arrests included the individual responsible for the attack on Colonial Pipeline last spring. While that attack was blamed on the Darkside ransomware group, it goes to show just how amorphous these groups are.
This event is very significant because it is believed to be the first time that Moscow has even admitted publicly that there are cyber-criminal elements operating out of, and residing in, Russia.
Many political analysts and cybersecurity groups are however calling this event a grandiose gesture aimed at the United States, during an obvious time of heightened tensions with Russia and Ukraine. Dmitri Alperovitch, co-founder and former CTO of CrowdStrike, and now Chairman of the Silverado Policy Accelerator had the following to say, “This is Russian ransomware diplomacy. It is a signal to the United States - if you don’t enact severe sanctions against us for invasion of Ukraine, we will continue to cooperate with you on ransomware investigations.”

Only time will tell if this move was a rare legitimate act of cooperation between two nations, or just a show in order to score some credibility. Many believe that the individuals arrested will spend days, rather than years behind bars, and may even be released the moment the United States imposes sanctions against Russia for their actions. This will be an interesting story to follow, that is for sure.
2. Ukraine State Websites Hit with Cyber Attack, Suggests Russian Involvement
Reuters reported last week that around 70 internet sites of Ukrainian government bodies were hit with a cyber-attack. The Ukrainians have said that they have evidence that Russia was behind the attacks, and that the purpose of the attack was to intimidate the country and erode the trust of the people in the Ukraine government.
This report was quickly followed by a Microsoft security blog detailing “a unique malware capability being used in intrusion attacks against multiple victim organizations in Ukraine.” The malware outlined in this blog post as used in this threat actor activity, is quite destructive indeed. The malware first overwrites the Master Boot Record (MBR) of the affected machine with a ransom note. This step is highly unusual for criminal ransomware gangs because it is so destructive to the computer in use. The goal of ransomware actors is to extract payment, and no one is going to pay if the computers they need to unlock are destroyed. As it turns out, this ransom note in the MBR is just a ruse. As the note is presented to the end user, Stage 2 of the malware executes and all files are then corrupted and overwritten by that next phase.
While the exact culprit behind the attack has not been identified, many are suggesting that a group dubbed UNC1151 is involved based on the calculus behind the tactics, techniques and procedures used. Per the linked Mandiant report from November, “Mandiant assesses with high confidence that UNC1151 is linked to the Belarusian government and with moderate confidence is linked to the Belarusian military.” Many will continue to monitor the threat intelligence behind these attacks over the coming weeks.
3. EU Police Agency, Europol, Forced to Delete Mass Amounts of Personal Data
Earlier this year, the European Data Protection Supervisor (EDPS) ordered Europol, the European Union Agency for Law Enforcement, to delete large masses of data concerning individuals with no established link to criminal activity. This enforcement action dates back to early 2019 when the EDPS first decided to open an inquiry into Europol based on its use of big data analytics. The EDPS is the EU’s independent data protection authority which supervises the processing of personal data by EU institutions bodies and agencies, including Europol.

This is an all to familiar faceoff between security and privacy, similar to that of the NSA’s mass surveillance systems of a decade ago. Many who are close to these findings and the Europol systems state that the volume of data that was on hand at Europol rivaled that of prior NSA programs.
The data in question held by Europol is data that it has received in datasets over the years from EU member states’ law enforcement authorities. The EDPS asserts that Europol has access to and maintains massive data sets that it has not properly analyzed. Europol should only be maintaining access to datasets that are clearly and directly linked to criminal activity that has occurred. EDPS also took issue with the length of time in which Europol has had access to this data without proper analysis or confirmation that it should be maintained or not. This order from the EDPS will ensure that data sets older than 6 months that have not gone through proper data subject categorization, will be erased.
This battle between security and privacy of individuals will continue to be a heated battle from both sides. As additional privacy laws and frameworks sprout across the world, these types of debates will only continue to intensify.