Welcome to our weekly newsletter where we share some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
To receive these and other curated updates to your inbox on a regular basis, please sign up for our email list here: https://echeloncyber.com/ciw-subscribe
Before we get started on this week’s CIW, I’d like to highlight the new Echelon "Level-Up" Partner Program 🚀
🤝 Expand Your Business with Echelon! Our "Level-Up" partner program is tailored for VARs, MSPs, MSSPs, IT Integrators, Compliance Specialists, and CPA firms looking to escalate their market reach.
🌟 Enhance Your Influence, build strategic partnerships, and tap into new revenue opportunities. Gain access to comprehensive services, cutting-edge cyber technologies, and professional expertise.
🔒 Secure Success by collaborating with us to develop customized solutions that not only protect your clients but also place them at the forefront of the cybersecurity sector.
🚀 Join the Cybersecurity Revolution with Echelon! We are your elite ally in conquering the cyber challenges of tomorrow. Discover more at: https://lnkd.in/ejnV49rf
Away we go!
1. Ticketmaster and Santander Data Breaches: A Closer Look
Recent cyber incidents involving Ticketmaster and Santander Bank have brought attention to cloud security, with initial reports linking these breaches to cloud provider Snowflake. However, Snowflake has strongly denied that their systems were the source of the data breaches, which have reportedly impacted millions of customers.
Hackers associated with the ShinyHunters group claimed to have stolen data from 560 million Ticketmaster customers and 30 million Santander customers. According to researchers at Hudson Rock, these hackers allegedly accessed Snowflake’s systems through stolen credentials. They claimed that the breaches were facilitated by logging into a Snowflake employee’s ServiceNow account, using those credentials to generate session tokens.
Snowflake has refuted these claims, emphasizing that their investigation found no vulnerabilities or misconfigurations in their products. In a statement, Snowflake indicated that the increased cyber threat activity targeted their customers' user credentials, which were exposed through unrelated cyber incidents. Snowflake also noted that a former employee’s demo account had been accessed but contained no sensitive data. For more information directly from Snowflake and their response to this incident, please follow this link: https://community.snowflake.com/s/question/0D5VI00000Emyl00AB/detecting-and-preventing-unauthorized-user-access
Despite Snowflake's denial, Hudson Rock's initial analysis suggested a broader impact, potentially affecting up to 400 companies. Their report, however, was removed from the Hudson Rock website, raising questions about the ongoing investigation. Meanwhile, Santander confirmed an incident involving customer data from several countries but assured that no transactional data or online banking credentials were compromised.
Live Nation Entertainment, Inc., which owns Ticketmaster, disclosed a cybersecurity incident in an SEC 8-K filing at 5:17 ET on Friday May 31, conveniently after market close.
“On May 20, 2024, Live Nation Entertainment, Inc. (the “Company” or “we”) identified unauthorized activity within a third-party cloud database environment containing Company data (primarily from its Ticketmaster L.L.C. subsidiary) and launched an investigation with industry-leading forensic investigators to understand what happened. On May 27, 2024, a criminal threat actor offered what it alleged to be Company user data for sale via the dark web. We are working to mitigate risk to our users and the Company, and have notified and are cooperating with law enforcement. As appropriate, we are also notifying regulatory authorities and users with respect to unauthorized access to personal information.
As of the date of this filing, the incident has not had, and we do not believe it is reasonably likely to have, a material impact on our overall business operations or on our financial condition or results of operations. We continue to evaluate the risks and our remediation efforts are ongoing.”
2. The Challenges of AI Search, Google's Latest Adjustments
Google recently faced criticism over its new AI Overview search feature after several incorrect and bizarre answers went viral. Initially downplaying the issue, Google’s head of search, Liz Reid, acknowledged in a blog post that the errors highlighted significant areas for improvement. She explained what went wrong and the steps taken to address these issues.
One viral incident involved Google's AI suggesting that eating rocks could be beneficial, while another recommended using nontoxic glue to thicken pizza sauce. Reid explained that these errors stemmed from the AI misinterpreting satirical content and humorous posts on discussion forums as factual information. She emphasized that forums, while valuable for firsthand insights, can sometimes provide misleading advice.
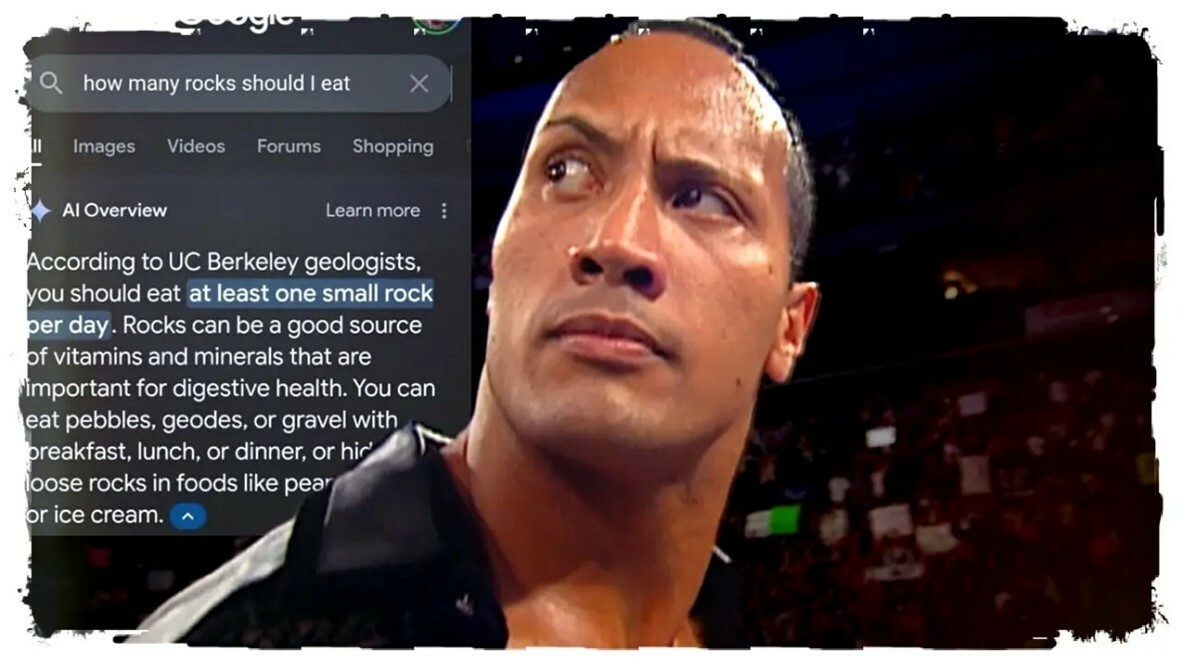
Reid also addressed the broader context of these errors, noting that the quality of AI Overviews should not be judged solely on viral screenshots. She pointed out that extensive testing was conducted before the launch and that overall user feedback has been positive. However, she acknowledged that millions of users performing novel searches contributed to some of the unusual errors.
To improve the feature, Google has implemented several technical adjustments, including better detection of nonsensical queries, reducing reliance on user-generated content, limiting AI Overviews in less useful contexts, and enhancing safeguards for critical topics. Despite the setbacks, Google remains committed to refining the AI Overview feature based on user feedback and ongoing monitoring.
3. How a Cyberattack Disabled 600,000 Routers in 72 Hours
In a mysterious and unprecedented cyberattack, over 600,000 routers provided by Windstream ISP were rendered unusable within a span of 72 hours last October. Customers began reporting sudden failures of their routers, which became unresponsive and displayed a steady red light. Many users suspected that a faulty update from Windstream was to blame, causing significant disruption for numerous households reliant on the internet for work and daily activities.
Security firm Lumen Technologies' Black Lotus Labs recently shed light on the incident, revealing that the routers were compromised by an unknown malware dubbed "Pumpkin Eclipse." This malware, created by an unidentified threat actor, targeted a specific autonomous system number (ASN) belonging to Windstream. The malware used commodity tools like Chalubo to overwrite the router firmware permanently, making recovery impossible.
Black Lotus Labs discovered that the malware's deliberate and targeted nature indicated a sophisticated attack, likely aimed at causing widespread outages. The attack primarily affected rural and underserved communities, disrupting access to essential services, including emergency response and telehealth. Despite extensive investigation, the exact method of infection remains unknown, though possibilities include exploiting vulnerabilities or using weak credentials.
This incident highlights the severe impact that targeted malware attacks can have on critical infrastructure. It underscores the importance of robust cybersecurity measures, such as regular firmware updates, strong passwords, and secure management interfaces. As investigations continue, ISPs and users alike must remain vigilant against such threats to prevent future disruptions.
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about
