Welcome to our weekly newsletter where we share some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
To receive these and other curated updates to your inbox on a regular basis, please sign up for our email list here: https://echeloncyber.com/ciw-subscribe
Before we get started on this week’s CIW, I’d like to highlight the new Echelon "Level-Up" Partner Program 🚀
🤝 Expand Your Business with Echelon! Our "Level-Up" partner program is tailored for VARs, MSPs, MSSPs, IT Integrators, Compliance Specialists, and CPA firms looking to escalate their market reach.
🌟 Enhance Your Influence, build strategic partnerships, and tap into new revenue opportunities. Gain access to comprehensive services, cutting-edge cyber technologies, and professional expertise.
🔒 Secure Success by collaborating with us to develop customized solutions that not only protect your clients but also place them at the forefront of the cybersecurity sector.
🚀 Join the Cybersecurity Revolution with Echelon! We are your elite ally in conquering the cyber challenges of tomorrow. Discover more at: https://lnkd.in/ejnV49rf

Away we go!
1. 49 Million Dell Customer Records Compromised
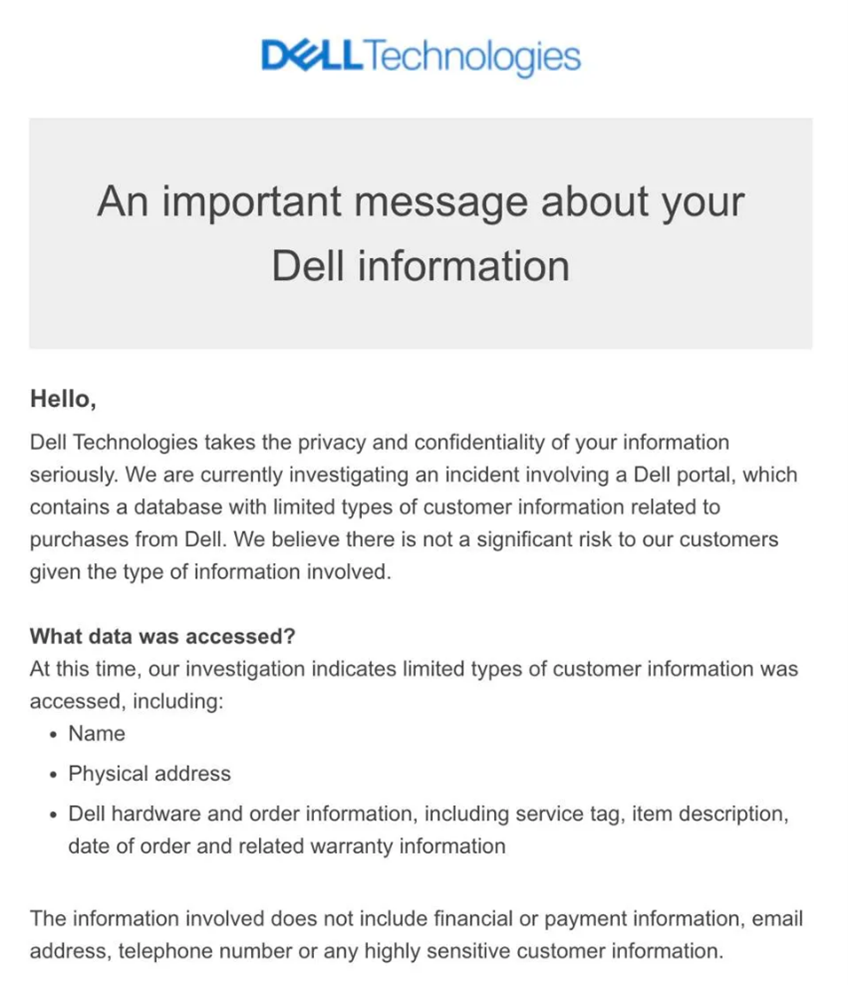
If you are a Dell customer and haven't checked your email recently, now might be a good time to do so. On the evening of May 9th, Dell sent out a notification about a security breach. The email, titled "An important message about your Dell information," might have landed in your spam or a folder for messages needing a second look. The message starts with a friendly greeting but quickly shifts to a more serious tone, revealing that a Dell portal containing a database with customer information was compromised.
The breach is still under investigation, and Dell's email emphasizes that the incident involves limited types of customer data. According to Dell, the compromised information includes names, physical addresses, Dell hardware, order details, and related warranty information. However, Dell reassures its customers that there is no significant risk as financial details, email addresses, and phone numbers were not part of the breach. Despite these assurances, a report on a hacker forum claims that 49 million customer records, including data on purchases made between 2017 and 2024, are being sold.
This situation presents a real-world risk, particularly for targeted phishing attempts. Information like names and order details could be used by malicious actors posing as Dell representatives to trick customers into providing sensitive information. Dell has advised customers to remain vigilant and report any suspicious activities related to their Dell accounts or purchases. Dell's cybersecurity program, designed to mitigate risks, promptly responded to the breach by implementing containment measures, starting an investigation, and notifying law enforcement.
A Dell spokesperson reiterated the company's commitment to customer security, explaining that their cybersecurity program includes prompt threat assessments and responses. While the investigation continues, Dell is working with external forensic specialists and monitoring the situation closely to protect customer information. Although Dell has not disclosed the exact number of affected customers, they assure that proactive steps are being taken to notify those impacted appropriately.
2. Justice Department Cracks Down on North Korean IT Worker Fraud
The Justice Department recently made several arrests connected to a sophisticated identity theft scheme orchestrated by North Korea. This scheme, which has generated significant funds for the North Korean government, involves thousands of North Korean IT workers using stolen identities to secure remote jobs at major U.S. companies. These jobs, unbeknownst to the employers, provided access to sensitive data and substantial salaries, all while the workers operated from abroad.
According to Justice Department officials, the fraud capitalizes on the convergence of a tech labor shortage in the U.S. and the rise of remote work. North Korean workers, using stolen American identities, were able to integrate into U.S.-based companies, thereby evading sanctions and funneling money back to North Korea, including its weapons programs. The initiative to counter this scheme began in March, with the Justice Department seizing several domains used by the North Korean IT workers last year.
One notable arrest is that of Christina Marie Chapman from Arizona, who allegedly facilitated the scheme by validating stolen identities and managing operations that connected overseas workers to U.S. company networks. Chapman is accused of running "laptop farms" where companies unwittingly sent equipment and paychecks, thinking they were for legitimate employees. Her activities reportedly helped generate over $6.8 million for the North Korean workers.
Additionally, the Justice Department has arrested other individuals, including Oleksandr Didenko from Ukraine and Minh Phuong Vong from Vietnam, for their roles in creating fake accounts and fraudulently obtaining jobs. The FBI has issued a public warning to companies, emphasizing the importance of robust identity verification processes to prevent such fraud. The State Department has also offered rewards for information on specific North Korean IT workers involved in this scheme.
3. CISA Insider Reveals Critical Vulnerabilities in U.S. Telecom Networks
On May 16, 2024, a senior cybersecurity official from the Cybersecurity & Infrastructure Security Agency (CISA) revealed alarming details about recent mobile network attacks in the U.S. The official disclosed that vulnerabilities in the SS7 and Diameter protocols have been exploited to track individuals' locations. These attacks have persisted despite assurances from major telecom companies like AT&T, Verizon, and T-Mobile that their networks are secure.
The statements, made in a filing to the FCC, indicate that these attacks are more widespread than previously acknowledged. They mentioned specific instances where individuals were tracked using these protocols, highlighting the ongoing risks to national security. The comments stand in stark contrast to the telecom companies' claims and underscore the need for more stringent security measures.
The revelations have prompted renewed calls for better protection of the telecommunications infrastructure. Senator Ron Wyden has been particularly vocal, urging the government to implement stricter cybersecurity standards. The FCC's recent public notice seeking expert input on the matter has further intensified the focus on these vulnerabilities.
The decision to speak out, seemingly without his agency's approval, underscores the severity of the issue. These insights provide a rare and unfiltered view of the challenges facing U.S. telecommunications security, emphasizing the need for immediate and robust action to safeguard against such threats.
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about