Welcome to our weekly post where I will be sharing some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
You can also Subscribe to receive Cyber Intelligence Weekly in your inbox each week.
Before we get started on this week’s CIW, I’d like to highlight an upcoming Tech Talk with Horizon3.ai on Wednesday, May 25, The Hackers Journey: Becoming an Ethical Hacker. In this talk, our very own James Stahl will speak with Noah King about common Windows attacks, starting with NTLM Relay. Many companies are vulnerable to NTLM Relay attacks, making it easy for emulated criminals to get and use domain user credentials, which can ultimately lead to full domain compromise. Sign up today to learn how this attack works and how to protect yourself against it!

Away we go!
1. Department of Justice Announces New Policy for Charging Cases under the Computer Fraud and Abuse Act
In a recent policy change, the Department of Justice announced that it will no longer charge those who are conducting good-faith security research. This move in policy direction is a win for security researchers, testers, and those operating with good intentions in mind. It wasn’t long ago that we were writing a story about how the Governor of Missouri wanted to jail a journalist for responsibly disclosing a website flaw in a state website.

Deputy Attorney General Lisa Monaco had this to say in a statement, “Computer security research is a key driver of improved cybersecurity. The department has never been interested in prosecuting good-faith computer security research as a crime, and today’s announcement promotes cybersecurity by providing clarity for good-faith security researchers who root out vulnerabilities for the common good.”
In the new policy, good-faith research is defined as: accessing a computer solely for purposes of good-faith testing, investigation, and/or correction of a security flaw or vulnerability, where such activity is carried out in a manner designed to avoid any harm to individuals or the public, and where the information derived from the activity is used primarily to promote the security or safety of the class of devices, machines, or online services to which the accessed computer belongs, or those who use such devices, machines, or online services.
This new policy is a big win for security professionals everywhere. Prior to this policy update, security researchers never knew what their fate might be if they were to call out a security vulnerability, now they finally have the air cover they deserve.
2. Flaw in Texas Website Exposed 1.8 Million Resident’s Data for Years
Speaking of website flaws, similar to the State of Missouri referenced above, the Texas Department of Insurance website exposed citizen data that was made publicly accessible for almost three years due to a “programming flaw.”

Per a document from the Texas State Auditor’s Department, “the confidential information at risk included claimants’ names, addresses, dates of birth, and phone numbers; part or all of their Social Security numbers; and information about injuries and workers’ compensation claims.”
The Texas Department of Insurance (TDI) notes on their website that while the audit found that the website and its data were exposed due to this flaw, there does not appear to be evidence to show that the information was misused in any way. This begs the question on whether there were sufficient logs one way or another to be able to come to such a conclusion. After all, TDI does note that they could not conclusively rule out that certain information on the web application was accessed outside of TDI.
3. Bada Bing, Bada Boom, Microsoft Bing’s Chinese Political Censorship of Autosuggestions in North America
A recent research study from The Citizen Lab at the University of Toronto shows that Microsoft’s Bing search engine filters out names of Chinese party leaders, dissidents, and other persons considered politically sensitive in China in its autosuggestions, effectively censoring these names from appearing. These reports come almost a year after Microsoft’s Bing search engine filtered out the “Tank Man” from China's violent crackdown on protests in Tiananmen Square in 1989 that depicts a man standing in front of an active tank in protest.

One of the most interesting findings of the report was noted in the key takeaways, “Using statistical techniques, we preclude politically sensitive Chinese names in the United States being censored purely through random chance. Rather, their censorship must be the result of a process disproportionately targeting names which are politically sensitive in China.”
The report notes that these names may be censored from the autosuggestion because Bing operates in China, and per legal reasons those politically charged names must be filtered out for searchers in the communist country. But this would not explain why the autosuggestion filtering is occurring the same way in the US.
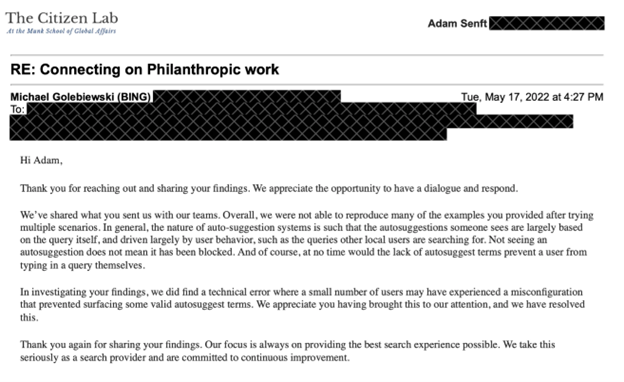
Microsoft did respond to The Citizen Lab’s query for comment and effectively stated that not seeing an autosuggestion doesn’t mean that something was blocked, and that autosuggestions are based on a number of other user and location-based factors. They did note that they found a “technical error” that may have prevented a small number of users from seeing some valid autosuggest terms.
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about