Welcome to our weekly post where I will be sharing some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
You can also Subscribe to receive Cyber Intelligence Weekly in your inbox each week.
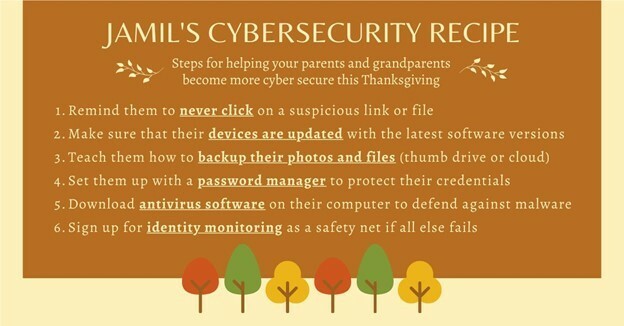
I hope everyone had a happy and healthy Thanksgiving holiday! Before we get started on this week’s CIW, I’d like to highlight this great post from the CISO at Equifax, Jamil Farshchi. Jamil shares some great tips on how we can help our friends and family become a little more cyber aware over the holidays! Thanks for the great tips Jamil! It certainly reminded me to think of my friends and family over the holiday.
Away we go!
1. GoDaddy Announces Security Incident Affecting Managed WordPress Service
Last week, GoDaddy released a statement through the SEC noting that they discovered an unauthorized third-party that gained access to their managed WordPress service. Through this incident, GoDaddy said that the data of up to 1.2 million of its customers was exposed.
As part of the SEC notice, GoDaddy mentions that the email address and customer number were exposed for over 1.2 million customers. In addition, sFTP and database user names and passwords were exposed, the original WordPress Admin password was exposed, and for a subset of customers, the SSL private key was exposed. GoDaddy noted that they changed any passwords that may have been exposed and they are in the process of installing new SSL certificates for customers where they may have had the SSL private key exposed.
Demetrius Comes, GoDaddy's Chief Information Security Officer had this to say in the SEC statement, "We are sincerely sorry for this incident and the concern it causes for our customers. We, GoDaddy leadership and employees, take our responsibility to protect our customers’ data very seriously and never want to let them down. We will learn from this incident and are already taking steps to strengthen our provisioning system with additional layers of protection.".

GoDaddy noted that the incident dates to September 6, 2021, and that the threat actor used a “compromised password” to gain access to a provisioning system in their legacy codebase for Managed WordPress. They did not explain the “compromised password” issue any further, however, as we all know, passwords are often the root of many cybersecurity ailments. Issues like password reuse, weak/guessable passwords, lack of multi-factor authentication are just a few common issues that rear their head in access management related breaches.
2. Apple Sues NSO Group to Curb the Abuse of State-Sponsored Spyware
This past week, Apple announced that they filed a lawsuit against the NSO Group and its parent company, to “hold it accountable for the surveillance and targeting of Apple users.” The NSO group has been in the headlines a good bit lately for not so good reasons. A few weeks back we wrote about how the US government added the NSO Group and their software to a Department of Commerce blacklist. Also, earlier this year, the Citizen Lab at the University of Toronto uncovered the ‘FORCEDENTRY’ exploit that was being used to remotely exploit and infiltrate Apple devices with NSO’s Pegasus spyware.
Craig Federighi, Apple’s senior vice president of Software Engineering, said the following in a prepared statement, “State-sponsored actors like the NSO Group spend millions of dollars on sophisticated surveillance technologies without effective accountability. That needs to change. Apple devices are the most secure consumer hardware on the market — but private companies developing state-sponsored spyware have become even more dangerous. While these cybersecurity threats only impact a very small number of our customers, we take any attack on our users very seriously, and we’re constantly working to strengthen the security and privacy protections in iOS to keep all our users safe.”
Apple’s senior director of commercial litigation Heather Grenier said in a statement to The New York Times that the lawsuit is meant to be a “stake in the ground, to send a clear signal” that the company won’t allow its users to suffer such egregious privacy abuse. As far as its basis for the suit, Apple’s argument is laid out in the complaint and basically states that NSO violated Apple’s terms of service because the group created hundreds of Apple IDs falsely, and did so to help it send data to targets.
The complaint notes, "The Court has personal jurisdiction over Defendants because, on information and belief, they created more than one hundred Apple IDs to carry out their attacks and also agreed to Apple’s iCloud Terms and Conditions (“iCloud Terms”), including a mandatory and enforceable forum selection and exclusive jurisdiction clause that constitutes express consent to the jurisdiction of this Court."

Apple also mentioned as part of their announcement that they are going to contribute at least $10 million, as well as any damages awarded from the lawsuit, to organizations that pursue cybersurveillance research and advocacy, such as the Citizen Lab. Apple also commits specifically to the Citizen Lab that it will provide pro-bono technical, threat intelligence, and engineering assistance to aid in the fight against sophisticated attacks on human rights. Much like the mission statement at Echelon, Apple notes in their statement that “Apple believes privacy is a fundamental human right, and security is a constant focus for teams across the company.” I have to say, it is certainly encouraging to see an organization with the resources of Apple to take a principled stand to defend the privacy rights of their customers in this way.
3. Brian Krebs Rings Alarm Bell on Zelle Fraud Scam for a Second Time
When Brian Krebs believes a scam alert is worthy of not one, but two articles on his website, it catches my attention. Krebs first posted about the Zelle cash out scams back on November 10, 2021 and just recently called it out again.
Zelle is a third-party application that allows users to send money back and forth in a peer-to-peer manner. It has become popular with many financial institutions as a good alternative to PayPal or Venmo, as it can keep financial institution customers on their platform. The problem is, many customers don’t realize they have Zelle. In most cases customers have never even used Zelle, but it is sitting there in their account and active by default.

Lately, fraudsters have been using various social engineering tactics to attempt to drain users bank accounts using a fake Zelle alert to initiate the scam. Krebs’ second article on the issue goes into great detail on the attack and how to spot it, but it goes something like this:
- Scammer sends out a fake Zelle message asking the customer if they attempted a payment of a large amount through Zelle.
- The customer will respond yes or no (which doesn’t matter), and they will then receive a call from the scammer, pretending to be from the fraud department of the customer’s financial institution.
- The scammer asks to verify the identity of the customer by sharing their user ID for their online banking.
- With knowledge of the user ID the scammer then uses the forgot password feature on the financial institution website and asks the customer to read them the two-factor passcode that gets sent.
- The scammer then resets the customers password themselves!
- Volia! The scammer is now in the account and will initiate funds transfers using Zelle to send the funds to the scammers accounts.
As far as what to do and how to combat these types of scams, Krebs mentions some great advice in his second article, “Remember the mantra: Hang up, Look Up, and Call Back. If you receive a call from someone warning about fraud, hang up. If you believe the call might be legitimate, look up the number of the organization supposedly calling you, and call them back.”
In the spirit of helping our friends and family this holiday season, let’s spread the word about scams like these and how we can be smart the next time we receive that angst inducing text that tempts us into doing something we shouldn’t!