Welcome to our weekly newsletter where we share some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
To receive these and other curated updates to your inbox on a regular basis, please sign up for our email list here: https://echeloncyber.com/ciw-subscribe
Also, we are always looking for great people to join our team. If you know anyone who fits the profiles for any of our open positions, drop me a line and let me know!
Before we get started on this week’s CIW, I’d like to highlight our very own Dahvid Schloss, Managing Lead of Offensive Security, who will be presenting at Wild West Hackin’ Fest along with a star-studded group that will pit Red Teamers vs. Blue Teamers for a wonderful Purple discussion! Click here to register today!

Away we go!
1. Mudge Testifies In Front of Senate Judiciary Committee
A couple of weeks ago we wrote about the shocking story of Twitter’s former cybersecurity chief, Peter Zacko, aka Mudge, who blew the whistle on several alleged major security weaknesses within social media giant Twitter. This past week, Mudge appeared in front of a Senate Judiciary Committee to testify about these allegations. The entire testimony can be viewed online.

During this testimony, Mudge alleged that Twitter is and has been extremely vulnerable to infiltration and exploitation of foreign government operatives, including China and India. When Mudge allegedly raised these concerns to a top executive, Mudge noted that the executive’s reply was, “Well, since we already have one, what is the problem if we have more? Let's keep growing the office.”
Mudge also alleged that Twitter is not all that deterred by United States authorities such as the Federal Trade Commission (FTC) or other, citing that Twitter has “priced in” one-time fines and penalties that may be imposed upon them. Mudge also highlighted again the potential massive user access rights issues, noting that the majority of the company can access sensitive data and internal Twitter tools that should be much more restrictive. Twitter has denied the majority of Mudge’s claims to date, but hasn’t provided any evidence to the contrary thus far per multiple reports. It will be interesting to see what happens next in this saga.
2. UBER Hacked After Employee Suffers MFA Exhaustion
Speaking of Twitter, it was abuzz with the news of Uber being hacked in a major way this past week. A hacker alerted Uber that it was in their systems when they posted in Uber’s Slack channel on Thursday, “Hi @here I announce I am a hacker and Uber has suffered a data breach.” The attacker also shared screenshots showing access to numerous internal systems at Uber, including AWS, Sentinel One EDR, GDrive, vCenter and more.
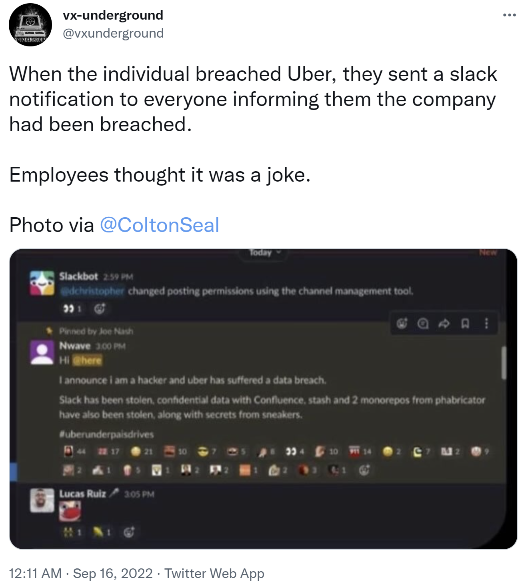
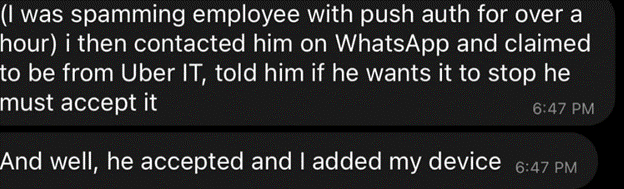
The Uber hacker supposedly was able to breach Uber’s defenses by targeting a single employee and spamming them with multi-factor authentication brute force attempts until they gave in. At that point, the threat actor was able to then access the environment.
Uber stated they took some of their internal systems offline as a precaution, but those systems have since been brought back online. Uber’s newsroom was fairly vanilla on the matter, stating “We have no evidence that the incident involved access to sensitive user data (like trip history). All of our services including Uber, Uber Eats, Uber Freight, and the Uber Driver app are operational.”
These types of “MFA fatigue” attacks have been extremely popular as of late, and have illustrated the downfall of certain types of MFA technologies and how they can be circumvented through such attacks. Once the attacker was in, they were able to quickly and easily access some of the most sensitive systems in the company with little in their way. All the more reason why the concepts of zero-trust are so important to implement both from an un-authenticated, but perhaps more importantly, an authenticated standpoint as well. It will be interesting to see how this story shakes out.
These types of “MFA fatigue” attacks have been extremely popular as of late and have illustrated the downfall of certain types of MFA technologies and how they can be circumvented through such attacks. Once the attacker was in, they were able to quickly and easily access some of the most sensitive systems in the company with little in their way. All the more reason why the concepts of zero-trust are so important to implement both from an un-authenticated, but perhaps more importantly, an authenticated standpoint as well. It will be interesting to see how this story shakes out.
3. Three Iranian Nationals Charged with Hacking and Conspiracy by DOJ
In an indictment that was unsealed last week, the Department of Justice alleged that three Iranian nationals conspired together to gain unauthorized access to computer networks and systems of hundreds of victims in the United States, the United Kingdom, Israel, Iran, and elsewhere, causing disruption, downtime and potential losses to their victims.
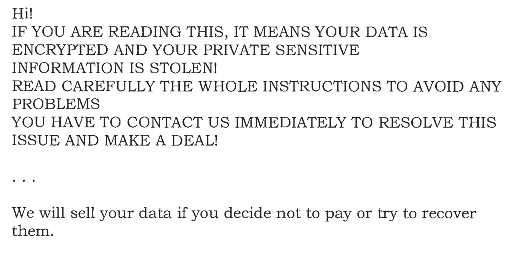
The indictment shares some details about the various victim’s that the group allegedly targeted, “The defendants also compromised, and often encrypted and extorted, hundreds of other victims, including an accounting firm based in Illinois; a regional electric utility company based in Mississippi; a regional electric utility company based in Indiana; a public housing corporation in the State of Washington; a shelter for victims of domestic violence in Pennsylvania; a County government in Wyoming; a construction company located in the State of Washington that was engaged in work on critical infrastructure projects; and a state bar association.”
In the above ransom note that the attackers sent to an accounting firm, the attackers note how they first stole the accounting firm’s data but also encrypted it as well. These types of double extortion tactics are now commonplace with most ransomware actors as it gives them several options to extort their victims. The indictment also noted that they used Bitlocker, Microsoft’s own tool, to encrypt their victim’s infrastructure. As you can see, ransomware and state backed/allowed cyber crime is still alive and well. It will be interesting to see if attacks such as this are covered in the tightening cyber insurance market of the future where state-backed exclusions are now becoming commonplace.
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about