
This article is part of our Bite-Sized Cyber Essentials Guide, which is designed to help anyone understand the essential information they need to incrementally level up privacy and security - at work and at home.
Multi-Factor Authentication
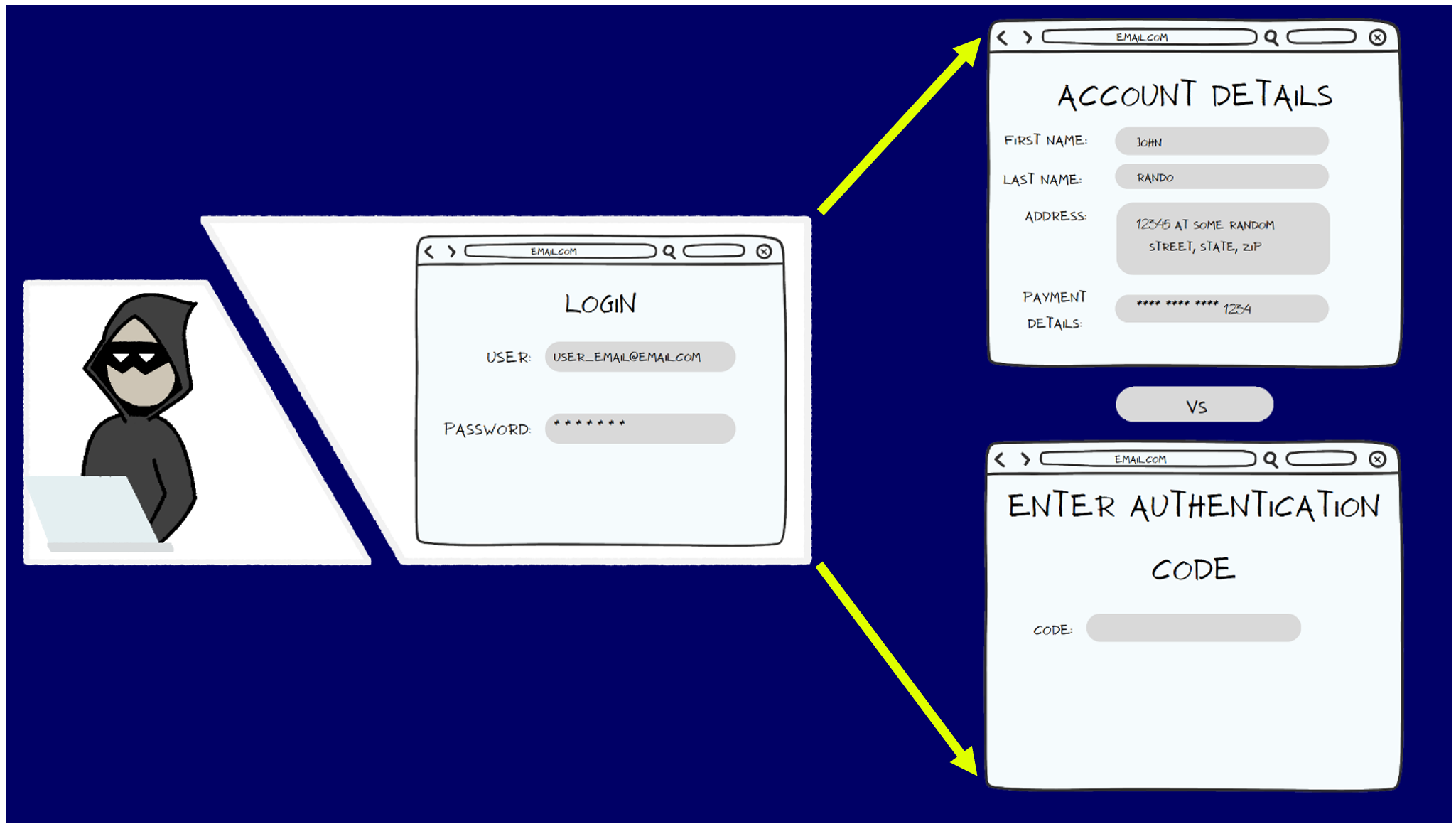
When users only require a single password to enter their account, this is what is called Single Factor Authentication. Multi-factor authentication (MFA) is the process of having more than one form of authentication to ensure that if one methods is compromised, an attacker is still unable to access the account.
Authentication has matured and changed in terms of how many forms of authentication there are. Currently, authentication is structured into the following categories:
SOMETHING YOU HAVE | SOMETHING YOU ARE | SOMEWHERE YOU ARE | |
|
|
|
|
As MFA is becoming more encouraged to ensure account security, the common forms of MFA that sites will support are the following:
Authentication codes sent via SMS | Randomized, timed, one time codes (TOTP) - typically through an app | Physical USB keys that only the holder can use to authenticate |
| SMS authentication is not the strongest solution, but it is still better than nothing! | TOTP from dedicated 2-factor authentication (2FA) apps are extremely convenient and offer fair security. | Physical USB keys offer very good security, with some mild inconvenience. |
| RISK:
SMS is not encrypted, consequentially, there is the risk that the codes received through text can by intercepted and used. | RISK: Not all 2FA apps are built the same! Some 2FA apps attempt to lock you into their ecosystem by not allowing users to transfer codes to another 2FA app. Additionally, some 2FA apps do not use secure encryption protocols. | RISK:
Given they are physical keys, they can be lost, and unless there is a backup, the data is lost along with the key. |
Top Tips for MFA
Consider the following:
- MFA everything: if an account supports MFA, use it!
- Use MFA as an additional layer to secure passwords
- Back up your 2FA codes! It is an incredible inconvenience if there is no backup (Be aware, some 2FA apps do not provide a transferrable backup of 2FA codes to lock users into using only their app)
The following authentication apps are open source, maintain strong encryption, allow exports, and don't lock in users to their ecosystem. This is a representative list of authentication apps and is not meant as a recommendation or a comprehensive list. We’ve included it here to help our readers understand what types of features we recommend that you look for when evaluating the best authentication app for you.
 Aegis (Android) |  Ravio OTP (IOS) |  Yubikey |
Open source
Encrypted Vault
Highly rated
Supports multiple backup types | Open source
Encrypted Vault Highly rated Supports multiple backup types | Multiple secure functions
Fights against phishing
FIPS 140-2 validated
Highly rated |

