Our team works with a range of powerful tools to ensure you have the resources needed to protect your systems, data, and people. Tools include but are not limited to:
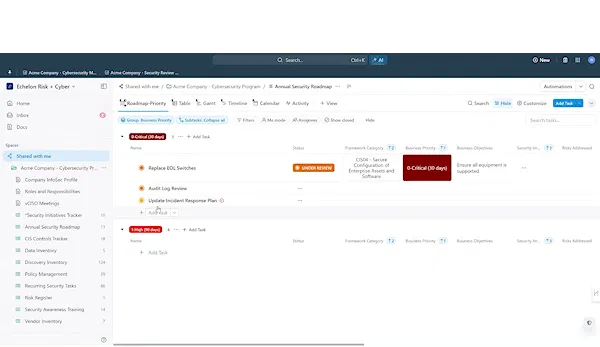
- Cybersecurity Management Portal for planning, tracking, and collaboration
- Endpoint Detection and Response (EDR) for monitoring and responding to threats on endpoints
- Managed Detection and Response (MDR) for continuous threat monitoring
- Security Information & Event Management (SIEM) to analyze security data and manage threats
- Cloud Security Posture Management (CSPM) to secure cloud infrastructure and ensure compliance
- Governance, Risk, Compliance (GRC) Platform to manage regulatory compliance and risk
- Security Awareness Training for educating employees on cybersecurity best practices
Other tools like identity and access management (IAM), automated penetration testing, and zero-trust services are available to meet specific needs.