Welcome to our weekly newsletter where we share some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
To receive these and other curated updates to your inbox on a regular basis, please sign up for our email list here: https://echeloncyber.com/ciw-subscribe
Before we turn to this week’s edition of Cyber Intelligence Weekly, I want to introduce a new CISO Spotlight Series: The Human Side of Cybersecurity.
This series is grounded in conversation rather than commentary. It centers on CISOs who are in the seat—navigating real leadership pressure, complex risk decisions, and the human realities of building and sustaining security programs. Some are earlier in their journey, others further along paths many of you may recognize or aspire toward. What they share isn’t theory. It’s experience—earned through moments of progress, frustration, growth, and reflection. These conversations are for the professionals who show up every day to quietly carry the weight of this industry.
Michael South (Dick’s Sporting Goods) — “Focus on the risks that support the business.”
In this episode, I sat down with Michael South, CISO at DICK'S Sporting Goods, whose 30-year career spans Navy service, public sector leadership, big tech, and now retail. Michael’s path is anything but linear—he started in Navy avionics, moved into IT, helped lead cybersecurity across Asia-Pacific for the U.S. 7th Fleet, served as Deputy CISO for the City of Washington, D.C., and later sharpened his cloud and security mindset at AWS and IBM. Along the way, he even lived the entrepreneur life—opening a coffee shop with his wife that landed “best local salad” and a top café ranking in its first year.
What stood out most was how Michael described his pull toward security: not one dramatic turning point, but breadcrumbs—from managing early enterprise systems to responding to real incidents like the Melissa virus era. He’s motivated by the investigative thrill of “beating them back,” and he sees a clear parallel between military service and cybersecurity: something bad happens, you respond—fast, calmly, and with purpose. That same mission mindset also shaped one of his proudest accomplishments: developing and exercising a Navy CONOPS for operating through a loss of satellite communications, treating “availability” as the often-overlooked pillar of security and proving resilience through real-world testing.
Michael also shared a leadership evolution that’s incredibly relevant right now. When he arrived at the City of D.C. in 2016, cloud adoption felt like chaos—too many compliance regimes, too much uncertainty, and a fear of losing control. His instinct was “no”… until he did the work to learn the cloud deeply. The result: he went from cloud skeptic to cloud advocate, and security ended up leading the city’s cloud adoption strategy—a perfect example of security as an enabler with guardrails, not a blocker with rules. His message connected directly to today’s AI moment: leaders can either be the “department of no” or they can learn fast, put guardrails in place, and help the business move responsibly.
Additional takeaways from the conversation:
- Data-driven, risk-informed security—with empathy. Michael’s operating philosophy is to protect the business without exhausting the humans doing the work.
- Stop manufacturing emergencies. Not every critical vulnerability is a five-alarm fire—risk has to be grounded in exploitability, real-world exposure, and business impact.
- Don’t create burnout with bad communication habits. Avoid non-urgent after-hours messages; use scheduled send; reduce “reply-all” noise and needless pressure.
- Bring teams together on purpose. Offsites, summits, and shared learning build trust—and trust makes hard asks easier when they truly matter.
- Empower the team to lead culture. Squads for onboarding, experience, and development create shared ownership and meaning beyond daily ticket queues.
- Being a CISO isn’t being the smartest technologist. The job is systems thinking, business alignment, and informing leadership so the company can make risk-based decisions.
- Post-quantum gets too much airtime for most businesses (today). Vendors and major tech platforms will solve the heavy lift; most organizations need to be ready to update and adopt when standards and products mature.
- Stay open to side quests. Michael’s “Bob Ross career” view—happy accidents plus readiness—encourages aspiring CISOs to pursue opportunities they didn’t plan for.
His billboard message to every new CISO is simple and grounding: Focus on the risks that support the business. Because security maturity isn’t built by chasing severity scores—it’s built by making smart tradeoffs, protecting your people, and consistently tying work back to what the organization actually values.
Watch the Full Video Here: https://youtu.be/NFbdRl0W_Eg

____________________________________
RSA 2026, Come Meet With Us!
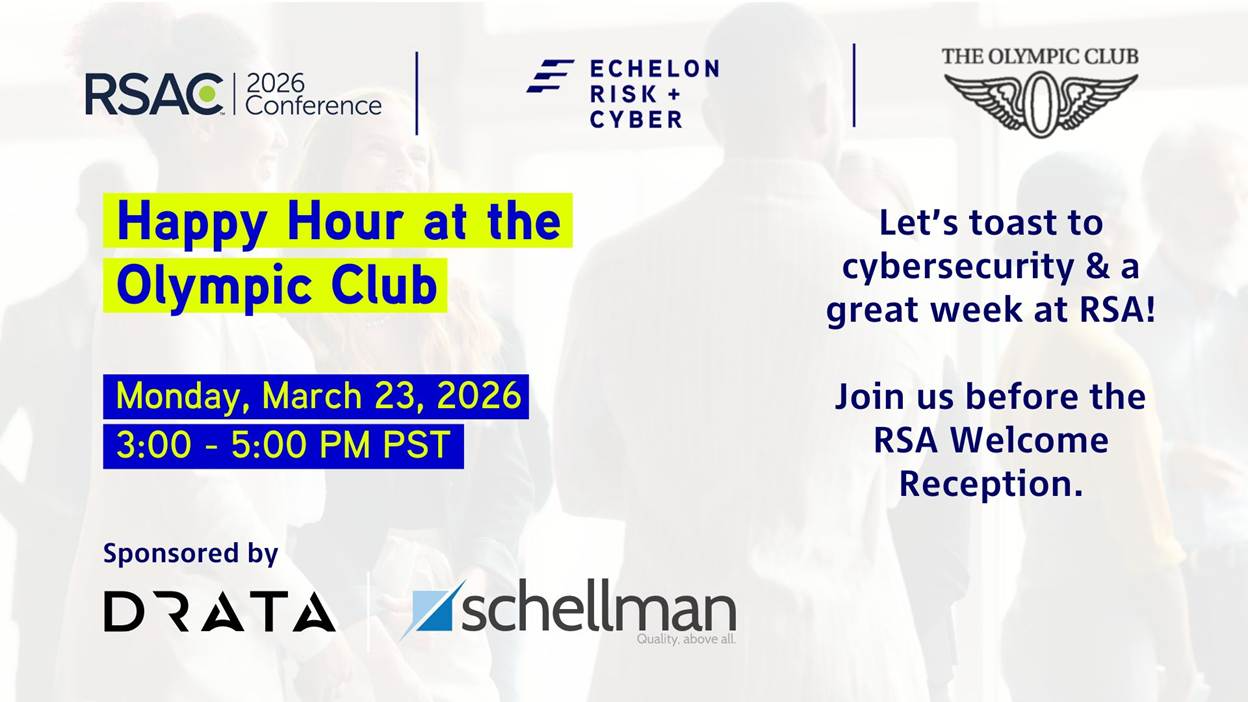
Also, to highlight upcoming events, we hope to meet you at RSAC 2026! If you are heading out to RSA and want to meet up with the Echelon team, come see us at our exclusive happy hour at the prestigious Olympic Club, a quiet oasis from the busy hustle and bustle of RSA.
Join Echelon Risk + Cyber for our annual RSA Happy Hour at The Olympic Club on Monday, March 23, from 3:00–5:00 PM PT, just before the official RSA Welcome Reception, with our sponsors Drata and Schellman!
Good people, great conversations, easy networking, no pressure.
📍 The Olympic Club, San Francisco
👉 Reserve your spot here: https://lnkd.in/enj3Q9D3
Away we go!
1. The 29-Minute Breach: What CrowdStrike’s 2026 Report Means for Security Leaders
The gold standard in threat intel, CrowdStrike’s 2026 Global Threat Report delivers a clear message for security leaders: attackers aren’t just getting smarter — they’re getting faster. The average “breakout time,” the window between initial access and lateral movement, has dropped to 29 minutes, down from 98 minutes just four years ago. In the fastest observed case, an adversary moved in 27 seconds. The implication is blunt: speed is now the defining characteristic of modern intrusions, and traditional detection-and-response timelines are increasingly outmatched.

But velocity is only part of the story. The report shows that 82% of detections were malware-free, with attackers operating through valid credentials, trusted identity flows, SaaS integrations, and legitimate system tools. In other words, adversaries are no longer breaking in — they’re logging in. Identity, cloud platforms, and software supply chains have become primary attack paths, allowing threat actors to blend into normal business activity and move without triggering traditional defenses.
Several trends reinforced this shift in 2025. Cloud intrusions rose 37% year over year, with a 266% spike from nation-state actors. Zero-day exploitation increased 42%. Supply chain attacks expanded beyond software updates into developer credentials and SaaS environments. Meanwhile, ransomware groups increasingly pursued cross-domain intrusions, targeting unmanaged assets like VPNs, firewalls, personal accounts, and third-party systems to bypass endpoint protections entirely. Even AI systems entered the threat landscape — both as targets and as tools used by attackers.
The takeaway for executives is less about any single tactic and more about the direction of the battlefield. The modern attack surface is identity-centric, cloud-native, and distributed across trusted systems. Organizations that still think in terms of endpoints and perimeter defenses are defending yesterday’s environment. The priorities now are clear: harden identity, eliminate blind spots between environments, aggressively manage vulnerabilities and edge devices, govern AI use, and train teams to respond at machine speed. In a world where attackers can move in under half an hour, resilience is no longer about preventing compromise — it’s about how quickly you can see it and stop it.

OneDrive Auto-Sync Turns SharePoint into Hidden Local Secrets Vaults
The Cloud Security Alliance published an analysis showing how OneDrive’s auto-sync feature can unintentionally replicate sensitive SharePoint document libraries onto local endpoints—often unmanaged contractor devices or BYOD machines without EDR, encryption, or compliance controls. Because SharePoint is widely used for document collaboration, sensitive data frequently resides in libraries that users casually sync to their desktops for convenience.
What organizations often overlook is that synced files behave like local data, bypassing many of the controls applied to cloud-resident content. DLP policies may not trigger, administrators lose visibility, and classification metadata may not carry over to local copies.
These synced folders become invisible storage zones—“secret vaults”—that attackers can exploit through endpoint compromise, data theft, or ransomware. Contractors without encrypted devices pose the greatest risk, as synced content remains stored locally even after access is revoked.
The issue magnifies when organizations rely heavily on external partners, project-based collaboration, or large distributed workforces. Without strict sync governance, organizations lose track of where sensitive data resides. The CSA stresses the importance of treating OneDrive sync as a data distribution mechanism, not a convenience feature, requiring policy governance, logging, and device-level controls.
Recommendations
- Disable auto-sync on sensitive SharePoint libraries.
- Require device encryption and EDR for any device syncing data.
- Enforce conditional access preventing sync to unmanaged endpoints.
- Monitor M365 audit logs for unusual or high-risk syncing behavior.

2. New Claude Code Flaws Highlight the Hidden Risks of Agentic Development
The rush to adopt AI-powered developer tools hit a reality check this week after Anthropic patched multiple security flaws in Claude Code, its agent-based coding assistant. Researchers from Check Point identified vulnerabilities that could allow attackers to execute malicious commands on a developer’s machine or quietly steal sensitive API keys — risks that highlight a growing blind spot in the emerging AI development ecosystem.
Two of the issues centered on how Claude Code handled project configuration files, particularly its automation “Hooks” and Model Context Protocol (MCP) settings. In affected versions, a malicious project could be crafted to trigger command execution before a user formally trusted the environment — effectively enabling remote code execution simply by opening an untrusted directory. A separate flaw allowed attackers to redirect API communications to a rogue endpoint, exposing plaintext API keys without obvious warning. While the technical mechanisms differed, the root issue was the same: implicit trust in project-level configuration.
Anthropic has since addressed the problems by strengthening permission prompts and blocking any command execution or network activity until users explicitly approve a project. But the broader lesson goes beyond a single product. As AI agents gain deeper access to local environments, development workflows, and cloud credentials, configuration files and project setup steps are becoming a new software supply chain attack surface — one that many organizations are not yet monitoring.
For security leaders, this is an early signal of what’s coming next. AI coding tools are powerful, but they operate with elevated trust and broad system access. That means traditional developer security practices — version control reviews, environment isolation, credential protection, and strict update discipline — now apply to AI agents as well. The productivity gains are real, but so is the risk. In the age of agentic development, the question isn’t just what code the AI writes — it’s what the AI is allowed to run.

Persistent Shadow AI Use Exposes Enterprises to Data Risks
Despite progress toward enterprise-approved generative AI tools, nearly half (47%) of users still access platforms like ChatGPT, Google Gemini, and Copilot through personal accounts outside organizational oversight, according to recent cloud security analytics spanning October 2024 to October 2025.
The analysis reveals a year-over-year drop in exclusive personal AI use from 78% to 47%, with approved accounts rising from 25% to 62%. However, a growing subset (9%, up from 4%) now switches between personal and corporate credentials, signaling gaps in usability or features that drive shadow IT behavior.
Unmonitored personal AI introduces a slew of vulnerabilities, such as: unsecured API connections to corporate servers, incomplete regulatory compliance, and doubled incidents of sensitive data uploads (~223 per company monthly), and creating entry points for hackers to exploit manipulated tools or exfiltrate proprietary information.
Shadow AI reflects employee workflows outpacing governance, where convenience outweighs policy and threatens to leave IT in the dark around data flows. The report frames this persistence as a defining 2026 threat vector, blending novel AI risks with classic visibility failures.
Organizations need to prioritize establishing AI governance frameworks with clear policies, simple provisioning of managed alternatives, and continuous monitoring of actual tool use to close these gaps before unchecked experimentation scales into widespread exposure.

3. Google Disrupts China-Linked Operation Targeting Telecoms Worldwide
Google recently announced the disruption of a large-scale cyberespionage campaign tied to a China-linked threat group that had quietly targeted telecommunications providers and government entities around the world for years. According to Google’s Threat Intelligence team, the operation impacted at least 53 organizations across 42 countries and reflects a long-term effort to gain strategic visibility into communications infrastructure and sensitive public-sector systems.
At the center of the campaign was a newly identified backdoor, known as Gridtide, designed for persistence and covert control. What made the activity particularly difficult to detect was the group’s use of legitimate cloud services — specifically Google Sheets — to hide command-and-control traffic. By blending malicious instructions into normal cloud usage patterns, attackers were able to mask their activity as routine business operations. Researchers noted that this technique could easily be replicated using other cloud collaboration platforms, highlighting a broader challenge for defenders: when attackers live inside trusted services, traditional detection models lose effectiveness.
While investigators did not confirm large-scale data exfiltration in the disrupted environment, the placement of malware on systems containing sensitive personal and identity data raises concern. The targeting pattern aligns with known telecom-focused espionage objectives — gaining the ability to identify individuals, map relationships, monitor communications, and potentially access call records or interception capabilities. In other words, the value of the intrusion wasn’t immediate theft — it was long-term surveillance positioning.
Google and its partners have taken down the known infrastructure supporting the campaign, but the company expects the threat group to rebuild quickly. For security leaders, the lesson is increasingly clear: modern espionage isn’t loud or destructive. It’s patient, cloud-aware, and designed to blend into normal operations. As attackers continue to weaponize trusted platforms and global communications networks, visibility into cloud behavior and identity-driven activity is becoming just as critical as traditional perimeter defense.
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about