Welcome to our weekly post where I will be sharing some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
You can also Subscribe to receive Cyber Intelligence Weekly in your inbox each week.
Before we get started on this week’s CIW, I’d like to highlight several great career openings we have available on our website. We keep on growing at Echelon and if you feel that you are a good fit, please take a look! At Echelon, we have created an environment where we inspire each other to dream more, learn more, do more, and become more. Echelon is a welcoming home, for growth minded cybersecurity professionals that love helping others more than themselves.

Away we go!
1. Data Broker Is Selling Location Data of People Who Visit Abortion Clinics
Joseph Cox of Vice Motherboard reported last week about a data broker that is selling location data related to people who visit abortion clinics. This story obviously has huge significance right now since the leak of a proposed Supreme Court decision that is set to repeal Roe v. Wade.
SafeGraph is the name of the company that is collecting and selling the data. The Vice report postulates how the data could be used to track and target people who visit clinics, where they visit the clinics from, where they go after, and so on. Since the story ran, SafeGraph has pulled the data for sale from their website, and had this to say in a statement, “In light of potential federal changes in family planning access, we're removing Patterns data for locations classified as NAICS code 621410 (‘Family Planning Centers’) from our self-serve “shop” and API to curtail any potential misuse of its data.”
While SafeGraph states that they only sell “facts about places,” we all know that the data they are selling is only valuable because of the PEOPLE that the underlying data is tied to. Governments, companies and people buy this data because of that fact and what it reveals. Google actually banned SafeGraph and any apps from using their code back in June of 2021. Google confirmed this in the above linked story that they gave app developers seven days to remove the data harvesting SafeGraph code from their software development kit (SDK) or face enforcement action.
While the data points are not specifically tied to any one individual when purchased, if the location data is disaggregated and device-specific, it is nearly impossible to de-identify the data. Location data tied to a specific device has been proven that it is enough to figure out who someone is. Think about it this way, if you travel from your home to church every Sunday at the same time, it would be easy to identify that pattern and trace the GPS location data back to your home. Not convinced, check out this 2013 scientific study, “Unique in the Crowd: The privacy bounds of human mobility.”
It is downright scary that this level of data can be purchased by anyone with a credit card and used for whatever reason that someone wants. If you want to be super spooked, check out this story from August 2021 detailing how the State of Illinois bought precise geolocation data from SafeGraph on 40% of its population for analysis.
2. Nakasone Says Cyber Command Did Nine 'Hunt Forward' Ops Last Year, Including in Ukraine
U.S. Cyber Command and National Security Agency chief Gen. Paul Nakasone told an audience at Vanderbilt University that the U.S. collaborated on nine “hunt forward” operations with different countries last year. He shared this data point to illustrate how the U.S. is playing a critical role to help keep its allies safe in cyber space. These are countries that have asked for the assistance of the U.S. and we have responded to their calls. The story was detailed by CyberScoop last week.

General Nakasone also spoke of the conflict between Russia and the Ukraine, and he acknowledged that the U.S. traveled to Ukraine in December to help build additional resilience against a coming wave of cyber-attacks.
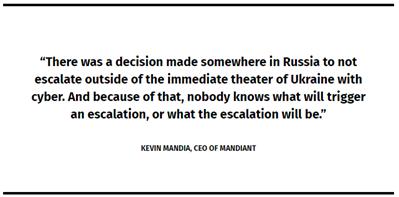
One of the biggest takeaways seemed to be the path forward regarding the Russian aggression in the Ukraine. Both General Nakasone and Kevin Mandia, CEO of Mandiant both talked about the perceived lack of cyber aggression beyond the localized conflict at this point.
Picture: CyberScoop
Per the story, both seemed to agree that the Russian’s have the capabilities, but nothing has triggered them to use those capabilities much more broadly just yet. Many believe that it is only a matter of time before they utilize their cyber prowess more broadly.
3. Heroku Recently Forced Customer Password Resets After GitHub OAuth Token Theft
According to an incident blog on Heroku’s website, on April 13, 2022, Salesforce Security was notified by GitHub that a subset of Heroku’s GitHub private repos were downloaded by a threat actor on April 9, 2022. Salesforce bought Heroku back in 2010.

Per the incident log details provided by Heroku, the threat actor obtained access to a Heroku database and stole stored customer GitHub integration OAuth tokens. They noted that access to the environment was gained by leveraging a compromised token for a Heroku machine account. The threat actor also downloaded a subset of Heroku private GitHub repos, containing Heroku source code.
A few days after the event, Heroku revoked all GitHub integration OAuth tokens and has since cut off access from GitHub altogether and don’t plan on reenabling the connection until ensuring the integration is secure.
Lastly, and possibly most concerning for customers of the service, Heroku noted in an update posted on May 5th that their investigation also revealed that the same compromised tokens were also leveraged to gain access to a database and were used to steal hashed and salted passwords for customers’ user accounts. The Salesforce Security team and Heroku are ensuring all customer passwords are reset, as well as internal Heroku credentials. This revelation comes weeks after they first learned of the incident at large.
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about