Welcome to our weekly newsletter where we share some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
To receive these and other curated updates to your inbox on a regular basis, please sign up for our email list here: https://echeloncyber.com/ciw-subscribe
Hackin' SaaS: Top 10 Vulnerabilities We Find, and How to Fix Them
Before we get started on this week’s CIW, I’d like to highlight Episode 2 of our "Hackin' SaaS: Top 10 Vulnerabilities We Find, and How to Fix Them" with hosts Kristofer Johnson and Evan Isaac!
🌐 Event Details
🗓️ Date: 20 Feb 2024
🕒 Time: 2 PM EST
Our esteemed hosts, @Kristofer Johnson and @Evan Issac, bring unparalleled expertise to this session. Having joined Echelon as interns over a year ago, they have rapidly ascended to consultant positions, thanks to their dedication and skill in the field of cybersecurity. Both hold certifications in penetration testing, demonstrating their proficiency and commitment to excellence.
Don’t miss out on this invaluable educational journey into SSRF vulnerabilities. Equip yourself with the knowledge to strengthen your software against potential threats. Sign up here: https://lnkd.in/em5VbQG4
I’d also like to highlight a solution from one of our strategic technology partners, Drata.
DRATA Compliance Automation & GRC Platform

Echelon Risk + Cyber proudly cultivates a diverse network of strategic relationships with leading vendors in the cybersecurity industry. These collaborations empower Echelon to deliver premium services to our clients through cutting-edge technology and valuable insights. In our ongoing effort to bring top-shelf knowledge, each week, we want to spotlight a distinguished partner solution offered at Echelon. This week’s focus is on Drata’s Compliance Automation and GRC Platform.
Drata’s Platform is a comprehensive governance, risk, and compliance (GRC) solution designed to streamline and automate the management of an organization's security and compliance processes. It offers a centralized hub for businesses to assess, monitor, and enhance the organization’s overall risk posture. The platform provides real-time visibility into an organization's security and compliance status, allowing for proactive risk mitigation and informed decision-making.
One key feature of Drata is its automated continuous monitoring capabilities, which enables organizations to stay vigilant against evolving security threats and regulatory changes. The platform automates the collection and analysis of data across various compliance frameworks (HIPAA, GDPR, ISO 27001, SOC 2, CMMC, PCI DSS, and more), ensuring that organizations can maintain compliance with industry standards and regulations. Drata's intuitive interface and customizable dashboards make it easy for users to track key performance indicators, monitor compliance status, and generate reports for audits or internal assessments.
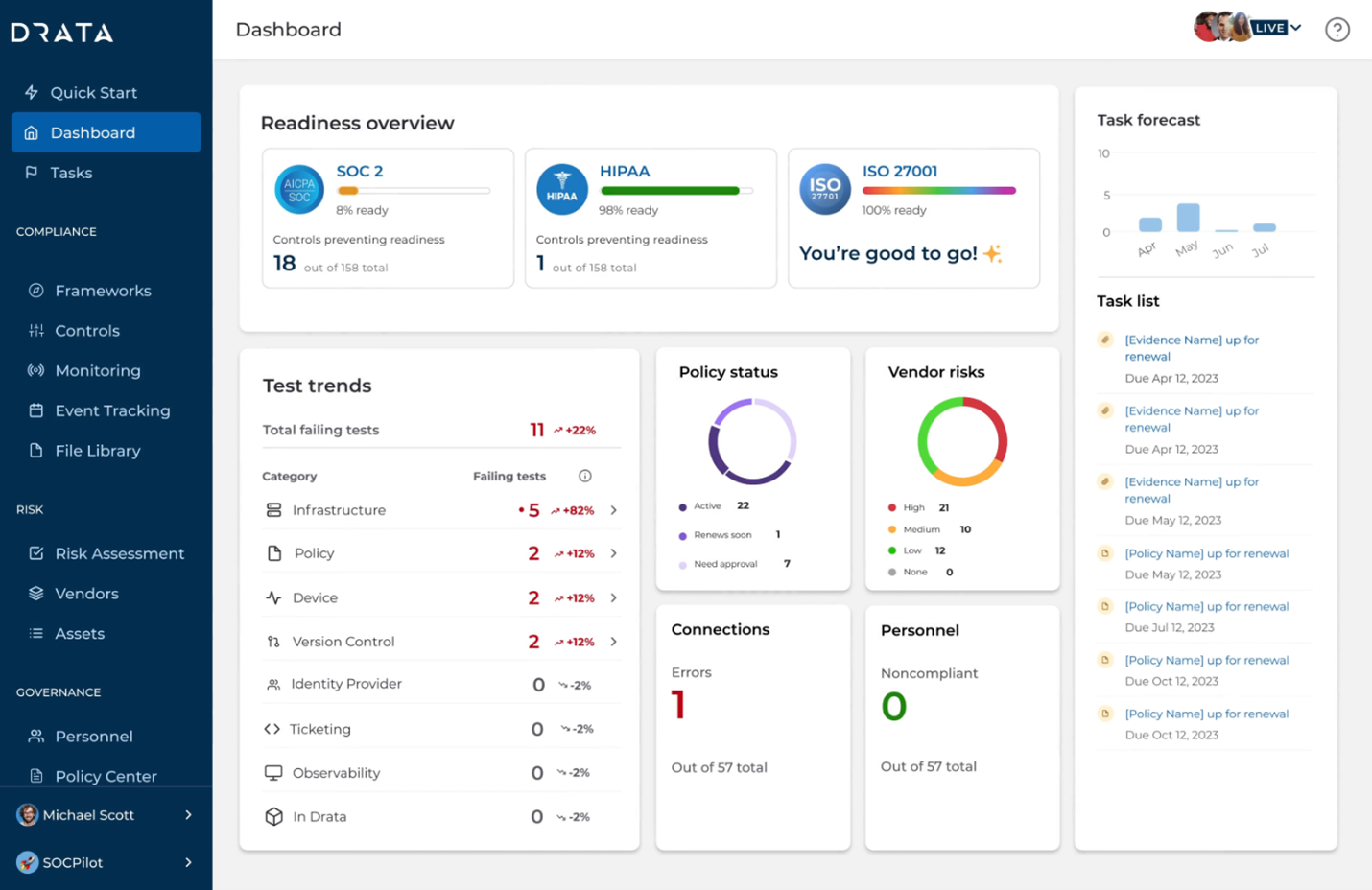
Furthermore, Drata’s Platform emphasizes simplicity and ease of use, making it accessible for both security experts and non-experts within an organization. The platform's automation capabilities significantly reduce the manual effort required for compliance management, allowing teams to focus on strategic initiatives rather than administrative tasks. With Drata, organizations can efficiently manage their GRC processes, fostering a proactive and resilient approach to security and compliance.
With the conclusion of the insight into Drata, we look ahead with anticipation. Echelon Risk + Cyber remains dedicated to pushing the boundaries of cybersecurity innovation, forging partnerships that empower us to stay at the forefront of industry trends. If your organization is grappling with specific security challenges, allow Echelon to help alleviate the burden. Reach out to discuss how we might help your organization and stay tuned for more solution highlights in the weeks to come!
Away we go!
1. Breach of Trust, U.S. Internet Corp.'s Unprecedented Email Privacy Fail
In a startling story by Journalist Brian Krebs, he shares how a Minnesota-based Internet provider, U.S. Internet Corp., has been found to have inadvertently exposed over a decade's worth of internal and customer emails to the public internet. This breach was discovered by cybersecurity firm Hold Security, which found a public link to a U.S. Internet email server that listed more than 6,500 domain names, each linking to the inboxes of individual users and employees, some dating back to 2008. U.S. Internet's Securence division, known for offering email filtering and security services to a global clientele including educational, government, and small business sectors, was implicated in this massive privacy oversight.
The exposure not only affected thousands of Securence clients but also revealed internal communications within U.S. Internet and its subsidiary, USI Wireless, including emails from the company's CEO, Travis Carter. The breach was promptly addressed after KrebsOnSecurity, who was alerted by Hold Security, contacted Carter with evidence of the leak. Carter's response indicated an investigation was underway, blaming the issue on a misconfiguration caused by a former employee's handling of the company's email server settings.
This incident raises serious concerns about U.S. Internet's capability to manage and protect sensitive email communications, highlighting a significant lapse in cybersecurity measures. The misuse of Securence's link-scrubbing service by hackers to redirect users to malicious sites adds another layer of complexity to the breach, underlining the need for stringent security practices and transparency from internet service providers. As U.S. Internet works to audit and secure its services, the breach serves as a cautionary tale about the importance of cybersecurity vigilance and the potential consequences of oversight (and perhaps a good case for continuous auditing).
2. Southern Water Cyberattack: Up to 470,000 Customers' Data Compromised
In a significant cybersecurity incident, Southern Water, a leading water utility in the South East of England, has confirmed that hackers compromised the personal data of up to 470,000 customers. This breach, resulting from a cyberattack in January, could affect "5 to 10 percent" of its customer base, as ongoing forensic investigations continue to assess the extent of the intrusion. Despite the company's reticence on the specific details of the stolen data, reports indicate that sensitive information including dates of birth, national insurance numbers, and bank details were accessed. The breach also extends to both current and some former employees of Southern Water, which employs around 6,000 individuals, indicating the broad scope of data vulnerability.
The attack was attributed to the Black Basta ransomware group, known for its connections to Russia and for previously targeting the U.K. outsourcing giant Capita. Black Basta claimed responsibility for stealing 750 gigabytes of sensitive data, including corporate and personal documents. Although Southern Water was listed on the ransomware group's dark web site, suggesting a ransom demand, the company has not disclosed whether it complied with any payment requests. Since the initial disclosure of the attack, Southern Water has been actively working with cybersecurity experts to monitor potential data leaks on the dark web, reporting no further evidence of the compromised data being published online.
This incident has prompted Southern Water to notify the affected customers and employees, alongside reporting the breach to the U.K.'s Information Commissioner's Office. The breach underscores the escalating threat of cyberattacks on critical infrastructure and the importance of robust cybersecurity measures to protect sensitive personal and corporate data.
3. Russia-Aligned Hackers Target Embassies in Sophisticated Cyber Campaign
A recent report has unveiled a sophisticated espionage campaign by a Russia-aligned hacking group, known as TAG-70, which has targeted European and Iranian embassies by exploiting a vulnerability in the Roundcube webmail server. This group, which also shows overlap with the Winter Vivern group, has been actively engaging in cyber-espionage aimed at gathering intelligence on European political and military strategies and Iranian diplomatic activities. Utilizing a cross-site scripting (XSS) vulnerability, identified as CVE-2023-43770, the hackers injected malicious scripts into trusted websites to spy on government and military agencies across Europe, as well as Iranian embassies in Russia and the Netherlands.
The Insikt Group from Recorded Future, who analyzed these attacks, highlighted the hackers' intentions to possibly gain strategic advantages or undermine European security. This campaign, which likely started in early October 2023, demonstrates the high level of sophistication and resources available to these threat actors, suggesting their operations are well-funded, possibly by Russian or Belarusian interests. The United States Cybersecurity and Infrastructure Security Agency (CISA) has recognized the seriousness of such vulnerabilities, including the Roundcube bug in its catalog of known exploited vulnerabilities, underscoring the significant risks they pose.
This espionage effort is part of a broader trend of Russian state-sponsored cyber activities targeting email services to gather intelligence, disrupt communications, and potentially compromise sensitive information related to Ukraine's defense and diplomatic efforts. Previous campaigns have seen similar groups, including BlueDelta and Fancy Bear, exploiting vulnerabilities in email services to conduct their malicious activities. This ongoing threat landscape highlights the critical need for heightened cybersecurity measures and vigilance among nations to protect against such sophisticated cyber threats.
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about