Welcome to our weekly newsletter where we share some of the major developments on the future of cybersecurity that you need to know about. Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
To receive these and other curated updates to your inbox on a regular basis, please sign up for our email list here: https://echeloncyber.com/ciw-subscribe
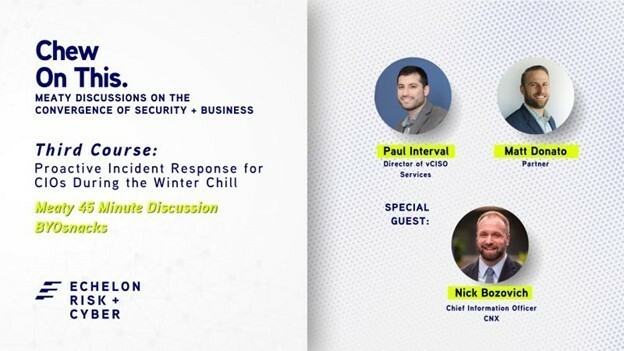
Before we get started on this week’s CIW, I’d like to highlight a festive "Chew On This" episode, unwrapping a crucial gift for CIOs and organizations — the wisdom of a proactive incident response strategy.
📅 Save the Date: Wednesday December 13, 2023
🕛 Time: 12:00pm EST
🎙️ Special Guest: Nick Bozovich with Echelon’s Matt Donato and Paul Interval
Discover how a proactive incident response strategy protects sensitive data, ensures compliance, preserves reputation, and reduces costs.
Our experts will guide you through adapting to evolving threats, ensuring business continuity, and maintaining trust amidst the holiday spirit. Don't miss this timely discussion blending security with the season.
Mark your calendar and fortify your organization for the challenges ahead! Register for the third course of Chew on This here: https://lnkd.in/eUdYQA8j
Away we go!
1. Microsoft Exposes North Korean Supply Chain Attack on Global Software
In a recent intelligence blog, Microsoft has exposed a sophisticated supply chain attack orchestrated by North Korean hackers. Dubbed 'Diamond Sleet', this hacking group, linked to the North Korean government, has been actively engaging in espionage, data theft, and network destruction. They target sectors like media, IT services, and defense globally. Their latest exploit involves a malicious tampering of a popular photo and video editing software installer developed by the Taiwanese company CyberLink, which Microsoft's Threat Intelligence team recently uncovered.
The hackers cleverly manipulated the CyberLink application installer, embedding a harmful code that, once triggered, downloads and launches a secondary, more destructive payload. This modified installer, deceptively signed with a valid CyberLink certificate, was cunningly hosted on CyberLink's own update infrastructure. It's designed to evade detection and has already impacted over 100 devices across various countries including Japan, Taiwan, Canada, and the United States. Microsoft detected suspicious activities starting from October 20 but hasn't observed any direct manipulation post-compromise.
The malware, named 'LambLoad', operates in a calculated manner. Before activation, it checks the date, time, and presence of specific security software. If conditions are unfavorable, it harmlessly runs the CyberLink software, avoiding the execution of its malicious segment. If not detected, it proceeds to download a second payload disguised as a .PNG file from three malicious domains. Microsoft linked these attacks to Diamond Sleet based on the malware's communication with previously compromised infrastructure by the group.
This incident is not isolated; Diamond Sleet has a history of deploying custom malware, weaponizing open-source software, and exploiting vulnerabilities. Their operations extend to compromising software build environments and attacking downstream victims. Microsoft has taken proactive steps, informing CyberLink and affected customers, and has blocked the malicious certificate. These revelations highlight the growing sophistication of supply chain attacks, a tactic increasingly favored by North Korean hackers.
2. FNF Cyber Incident Disrupting Real Estate Transactions Nationwide
Fidelity National Financial (FNF), a prominent Fortune 500 company known for its title insurance and settlement services in the mortgage and real estate sectors, recently disclosed a significant cybersecurity breach. In an alarming announcement made this Tuesday, FNF reported it fell victim to a cyberattack that severely affected its operational systems. This incident led to the company taking decisive action, as detailed in their report to the Securities and Exchange Commission (SEC). FNF has launched a comprehensive investigation into the breach, enlisting the aid of top cybersecurity experts. They've also informed law enforcement and have taken proactive steps to mitigate and contain the fallout of the attack.
One of the immediate responses by FNF was to restrict access to certain systems, a move that, while necessary for security, unfortunately caused considerable disruption in their services. This impacted various aspects of their business, particularly those relating to title insurance, escrow, and mortgage transactions. A key concern highlighted in their report is that an unauthorized party gained access to specific FNF systems and acquired sensitive credentials. As the investigation is still ongoing, the full extent and implications of the breach remain uncertain.
The repercussions of this cybersecurity incident have been far-reaching, significantly affecting FNF's business operations and clients. Real Estate News has reported major interruptions in scheduled property closings, leaving real estate agents and homebuyers in a state of distress as they search for immediate alternatives. Transactions are stalled, with systems necessary for their completion expected to remain offline for the time being.

In their blog, TechCrunch received insights from individuals connected to FNF, including one who revealed that the company opted for a complete shutdown of their network, systems, and even email services in an effort to cleanse their servers in Jacksonville and avert further complications. Another source in the IT sector confirmed the extent of the lockdown, stating that FNF's systems were completely inaccessible. This cyberattack not only underscores the vulnerability of major corporations to digital threats but also highlights the cascading effect such incidents can have on broader industries and individual consumers.
3. Citrix Bleed, Lessons from Boeing's Ransomware Situation
The US Cybersecurity and Infrastructure Security Agency (CISA), in collaboration with the FBI and the Australian Cyber Security Centre (ACSC), has detailed how the notorious LockBit ransomware gang exploited a critical vulnerability, known as Citrix Bleed, to attack aviation giant Boeing. This vulnerability, identified as CVE-2023-4966, affects Citrix NetScaler web application delivery control and NetScaler Gateway appliances. Its exploitation by both nation-state actors and groups like LockBit has raised serious concerns.

Citrix Bleed is particularly dangerous because it allows hackers to bypass password requirements and multi-factor authentication (MFA), leading to session hijacking of legitimate user sessions. This vulnerability grants attackers elevated permissions, enabling them to harvest credentials, access data, and move laterally within networks. Boeing's voluntary sharing of its experience with the LockBit ransomware attack has been crucial. It provided in-depth insights, enabling CISA and other agencies to issue comprehensive guidance and preventive measures to combat this threat.
The attack on Boeing demonstrated the sophisticated tactics used by cybercriminals. LockBit affiliates were able to access valid NetScaler session cookies, establishing an authentication session within the NetScaler appliance without requiring a username, password, or MFA token. This was achieved by exploiting a flaw in the HTTP Hoster header, leading to the leakage of system memory information, including the necessary cookie. Following this breach, LockBit used PowerShell scripts and deployed remote management tools like AnyDesk and Splashtop, culminating in the leak of approximately 40GB of Boeing's data. Fortunately, Boeing confirmed that flight safety was never compromised.
CISA, along with the FBI and the ACSC, are urging network administrators to apply recommended mitigations, such as isolating any NetScaler appliances and actively searching for malicious activities using the provided detection methods. The importance of applying Citrix’s patches, which have been available for over a month, is heavily emphasized. The fast nature of the Citrix Bleed timeline, from its disclosure to the consequential attacks, underscores the critical nature of cybersecurity vigilance and the ongoing battle against sophisticated cyber threats.
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about