Welcome to our weekly post where I will be sharing some of the major
developments on the future of cybersecurity that you need to know about.
Make sure to follow my LinkedIn page as well as Echelon’s LinkedIn page to receive updates on the future of cybersecurity!
You can also Subscribe to receive Cyber Intelligence Weekly in your inbox each week.
Before we get started on this week’s CIW, I’d like to highlight our very own Dahvid Schloss who was quoted in Dark Reading last week with his take on the ZuoRAT malware that has been infecting small office-home routers worldwide.
Away we go!
1. Florida Man Arrested for Selling $1 Billion in Fake Cisco Hardware on Amazon, eBay
U.S. prosecutors recently announced an indictment of a Florida man that has been accused of importing and selling counterfeit Cisco devices, under a set of entities known as the “Pro Network.” Onur Aksoy, 38 of Miami, ran a number of different online storefronts to peddle his fake wares for almost a decade. They purportedly sold tens of thousands of these devices over the years, totaling close to one billion dollars in retail value.

According to the indictment, the counterfeit devices were typically older models that were refurbished to look like newer Cisco models with pirated software and unreliable software and hardware components. The devices were then described as newer models and sold on various online storefronts to unsuspecting users. To make the devices look like new, the Chinese counterfeiters even added high-quality counterfeited Cisco labels, stickers, boxes, documentation, packaging, and other materials.
Users of these devices would eventually realize that the devices they received were fraudulent when they began to malfunction or fail. In many cases, when critical devices fail, they often cause much damage to networks and can cause significant business disruption to operations. Per the indictment, U.S. Customs and Border Protection (CBP) seized approximately 180 shipments of counterfeit Cisco devices being shipped to the Pro Network Entities from China and Hong Kong.
This story highlights the importance of third-party vetting and sourcing in today’s global economy. Secure sourcing of critical network components such as firewalls, routers, switches should be a critical component of any organizational security program.
2. Apple Unveils new “Lockdown Mode” to Protect Users from Targeted Spyware
Last week, Apple unveiled a preview of what they are calling “groundbreaking security capability” that is supposed to offer special additional protections in its operating system to prevent users from falling victim to state-sponsored style attacks using cutting edge spyware. Apple will be releasing the capabilities in the fall for a small amount of users with iOS 16, iPadOS 16, and macOS Ventura. They also announced a $10 million dollar grant to support organizations that investigate and expose the types of cyber attacks that use what they are calling “state-sponsored mercenary spyware.”
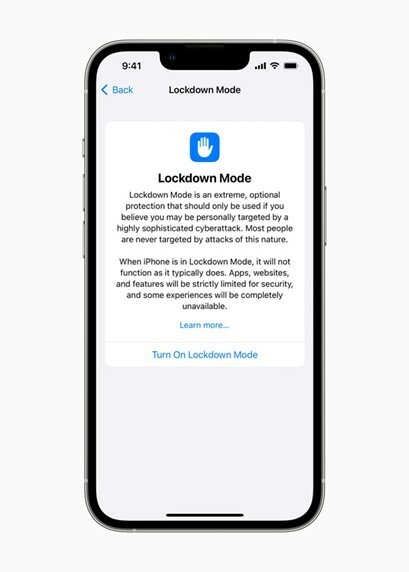
Photo: apple.com
We’ve written extensively in the past about highly targeted spyware attacks going after users phones, often times using the Pegasus Spyware from the NSO Group. These spyware attacks often circumvent protections on iPhone’s and are also very stealthy, requiring no action from the user typically. These zero-click attacks are so dangerous because the user’s phone may be become infected by the spyware and they have no idea that it has even occurred.
Ivan Krstić, Apple’s head of Security Engineering and Architecture had this to say about the new features, “Apple makes the most secure mobile devices on the market. Lockdown Mode is a groundbreaking capability that reflects our unwavering commitment to protecting users from even the rarest, most sophisticated attacks. While the vast majority of users will never be the victims of highly targeted cyberattacks, we will work tirelessly to protect the small number of users who are. That includes continuing to design defenses specifically for these users, as well as supporting researchers and organizations around the world doing critically important work in exposing mercenary companies that create these digital attacks.”
When launched, the Lockdown Mode feature will include the following protections:
- Messages: Most message attachment types other than images are blocked. Some features, like link previews, are disabled.
- Web browsing: Certain complex web technologies, like just-in-time (JIT) JavaScript compilation, are disabled unless the user excludes a trusted site from Lockdown Mode.
- Apple services: Incoming invitations and service requests, including FaceTime calls, are blocked if the user has not previously sent the initiator a call or request.
- Wired connections with a computer or accessory are blocked when iPhone is locked.
- Configuration profiles cannot be installed, and the device cannot enroll into mobile device management (MDM), while Lockdown Mode is turned on.
This is a huge statement from Apple, highlighting the importance of user privacy and protection for people that own their products. To be fair, Apple had protections in place prior to the Lockdown Mode, but these are new and enhanced efforts to combat these ever evolving sophisticated threats.
3. NFT Marketplace OpenSea Reports Massive Email Data Breach
One of the most popular NFT marketplaces in the world recently announced a data breach of user emails. A staff member at Customer.io, an email delivery vendor for OpenSea, misused their access to download and share mass troves of email addresses that users provided to OpenSea to open accounts as well or to receive their newsletter.

TechCrunch received a comment from Customer.io on the matter, they said, “After further investigating the compromised OpenSea email addresses incident, we have learned today that the email addresses from five other customers were also provided to the same external bad actor. We know this was a result of the deliberate actions of a senior engineer who had an appropriate level of access to perform their duties, and provided these email addresses to the bad actor. This action was limited to this single employee.”
The good news is that Customer.io does not have access to wallet addresses and does not appear to have the ability to steal NFT’s or access wallets in any way. The bad news is that bad actors now know who owns OpenSea accounts and can target those users over time with very well crafted phishing attacks and other types of clever social engineering ploys.
OpenSea recommends the following safety items to properly secure your account and NFTs:
- Be cautious of phishing emails from addresses trying to impersonate OpenSea. OpenSea will ONLY send you emails from the domain: ‘opensea.io.’ Please do not engage with any email claiming to be from OpenSea that does not come from this email domain.
- Never download anything from an OpenSea email. Authentic OpenSea emails do not include attachments or requests to download anything.
- Check the URL of any page linked in an OpenSea email. We will only include hyperlinks to ‘email.opensea.io.’ URLs. Make sure that ‘opensea.io’ is spelled correctly, as it’s common for malicious actors to impersonate URLs by shuffling letters.
- Never share or confirm your passwords or secret wallet phrases. OpenSea will never prompt you to do this – in any format.
- Never sign a wallet transaction prompted directly from an email. OpenSea emails will never contain links which directly prompt you to sign a wallet transaction. Never sign a wallet transaction that doesn’t list the origin of https://opensea.io if you were led there by email.
Thanks for reading!
About us: Echelon is a full-service cybersecurity consultancy that offers wholistic cybersecurity program building through vCISO or more specific solutions like penetration testing, red teaming, security engineering, cybersecurity compliance, and much more! Learn more about Echelon here: https://echeloncyber.com/about